Son kullanma tarihi geçmiş, bayatlamış bir tarayıcı kullanıyorsanız, Mercedes kullanmak yerine tosbağaya binmek gibi... Web sitelerini düzgün görüntüleyemiyorsanız eh, bi' zahmet tarayıcınızı güncelleyiniz.
Modern Web standartlarını karşılayan bir tarayıcı alternatifine göz atın.
Modern Web standartlarını karşılayan bir tarayıcı alternatifine göz atın.
Çözüldü Mavi ekran hatası
- Konuyu başlatan ygtrcys
- Başlangıç Tarihi
- Mesaj 13
- Görüntüleme 1B
Bu konu çözüldü olarak işaretlenmiştir. Çözülmediğini düşünüyorsanız konuyu rapor edebilirsiniz.
Çözüm
1) Aşağıdaki rehberi uygulayın ve sonuçları paylaşın.
2) İnternetten DDU yazılımını ve aşağıdaki driverı indirin. Hepsi indirilince DDU'dan ses kartını seçip onun altından da Realtek (WIP) seçeceksiniz. Daha sonra işlemi başlatacaksınız. Bilgisayar kapandıktan sonra bilgisayarın internet bağlantısını kesip bu size verdiğim linkteki driverı kuracaksınız.
2) İnternetten DDU yazılımını ve aşağıdaki driverı indirin. Hepsi indirilince DDU'dan ses kartını seçip onun altından da Realtek (WIP) seçeceksiniz. Daha sonra işlemi başlatacaksınız. Bilgisayar kapandıktan sonra bilgisayarın internet bağlantısını kesip bu size verdiğim linkteki driverı kuracaksınız.
Daha fazla
- Sistem Özellikleri
- i5-12400F, RTX 3070
- Cinsiyet
- Erkek
- Meslek
- Bilgisayar Mühendisliği öğrencisi
Minidump dosyanızı aşağıdaki rehberi okuyup paylaşırsanız yardımcı olabiliriz.
 www.technopat.net
www.technopat.net
Minidump Dosyalarını Paylaşın
Minidump dosyaları, bilgisayarınız mavi ekran verdiğinde belleğin ufak bir dökümünü barındıran dosyalardır. Bunları analiz ederek mavi ekran hatalarının nedenini öğrenebiliriz. Minidump dosyaları C:\Windows\Minidump klasöründe bulunur ve DMP uzantılıdır. Bu dosyaları sizden istediğimizde...
ygtrcys
Decapat
- Katılım
- 24 Ekim 2020
- Mesajlar
- 57
Daha fazla
- Cinsiyet
- Erkek
Minidump.rar
 drive.google.com
drive.google.com
Son düzenleyen: Moderatör:
- MemTest86 ile RAM'lerde test yapın.
- Hatalardan birine
nsiproxy.sysdiye bir dosya sebep olmuş. Ne olduğu araştırdım ancak net bir bilgi bulamadığımdan bir şey demeyeceğim. - Ses sürücülerinizi güncelleyin.
- HD Tune ile tüm sürücülerde "Error Scan" yaparsanız iyi olur. Ayrıca HDD Sentinel yazılımından ekran görüntüsü paylaşın.
Kod:
APC_INDEX_MISMATCH (1)
This is a kernel internal error. The most common reason to see this
bugcheck is when a filesystem or a driver has a mismatched number of
calls to disable and re-enable APCs. The key data item is the
Thread->CombinedApcDisable field. This consists of two separate 16-bit
fields, the SpecialApcDisable and the KernelApcDisable. A negative value
of either indicates that a driver has disabled special or normal APCs
(respectively) without re-enabling them; a positive value indicates that
a driver has enabled special or normal APCs (respectively) too many times.
Arguments:
Arg1: 00007ff92890be14, Address of system call function or worker routine
Arg2: 0000000000000000, Thread->ApcStateIndex
Arg3: 000000000000ffff, (Thread->SpecialApcDisable << 16) | Thread->KernelApcDisable
Arg4: ffffb48e705e9b80, Call type (0 - system call, 1 - worker routine)
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 3593
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-62N06FT
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 3585
Key : Analysis.Memory.CommitPeak.Mb
Value: 74
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 1
BUGCHECK_P1: 7ff92890be14
BUGCHECK_P2: 0
BUGCHECK_P3: ffff
BUGCHECK_P4: ffffb48e705e9b80
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: chrome.exe
STACK_TEXT:
ffffb48e`705e99b8 fffff806`44806569 : 00000000`00000001 00007ff9`2890be14 00000000`00000000 00000000`0000ffff : nt!KeBugCheckEx
ffffb48e`705e99c0 fffff806`44806433 : ffffcf0d`e6aa3080 ffffcf0d`e7618080 ffffb48e`705e9b18 ffffffff`fffd67f0 : nt!KiBugCheckDispatch+0x69
ffffb48e`705e9b00 00007ff9`2890be14 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceExitPico+0x1fe
00000082`e1fff7d8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ff9`2890be14
SYMBOL_NAME: nt!KiSystemServiceExitPico+1fe
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.572
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 1fe
FAILURE_BUCKET_ID: 0x1_SysCallNum_4_nt!KiSystemServiceExitPico
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {52cd694c-15ec-48c3-924a-3539560711db}
Followup: MachineOwner
---------
MULTIPLE_IRP_COMPLETE_REQUESTS (44)
A driver has requested that an IRP be completed (IoCompleteRequest()), but
the packet has already been completed. This is a tough bug to find because
the easiest case, a driver actually attempted to complete its own packet
twice, is generally not what happened. Rather, two separate drivers each
believe that they own the packet, and each attempts to complete it. The
first actually works, and the second fails. Tracking down which drivers
in the system actually did this is difficult, generally because the trails
of the first driver have been covered by the second. However, the driver
stack for the current request can be found by examining the DeviceObject
fields in each of the stack locations.
Arguments:
Arg1: ffffce0d435185f0, Address of the IRP
Arg2: 0000000000001232
Arg3: 0000000000000000
Arg4: 0000000000000000
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 3592
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-62N06FT
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 6547
Key : Analysis.Memory.CommitPeak.Mb
Value: 76
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 44
BUGCHECK_P1: ffffce0d435185f0
BUGCHECK_P2: 1232
BUGCHECK_P3: 0
BUGCHECK_P4: 0
IRP_ADDRESS: ffffce0d435185f0
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: Dragon.exe
STACK_TEXT:
ffffb887`79a2e688 fffff805`0c865934 : 00000000`00000044 ffffce0d`435185f0 00000000`00001232 00000000`00000000 : nt!KeBugCheckEx
ffffb887`79a2e690 fffff805`0c6c2fd7 : 00000000`00000000 00000000`00000002 00000000`00000070 ffffce0d`43518628 : nt!IopfCompleteRequest+0x1a2944
ffffb887`79a2e780 fffff805`1bb12714 : 00000000`00000000 ffffce0d`435186c0 ffffce0d`435185f0 0000004e`66eff5c0 : nt!IofCompleteRequest+0x17
ffffb887`79a2e7b0 fffff805`0c6cd805 : 00000000`00000002 00000000`00000000 ffffce0d`44954800 ffffce0d`3e37f060 : nsiproxy!NsippDispatch+0xb4
ffffb887`79a2e800 fffff805`0cac2528 : ffffce0d`435185f0 00000000`00000000 00000000`00000000 00000000`00000001 : nt!IofCallDriver+0x55
ffffb887`79a2e840 fffff805`0cac1df5 : 00000000`00000000 ffffb887`79a2eb80 00000000`00040800 ffffb887`79a2eb80 : nt!IopSynchronousServiceTail+0x1a8
ffffb887`79a2e8e0 fffff805`0cac17f6 : 00000000`00000001 00000000`00000dbc 00000000`00000000 00000000`00000000 : nt!IopXxxControlFile+0x5e5
ffffb887`79a2ea20 fffff805`0c805fb8 : ffffce0d`4427f080 0000004e`66eff4a8 ffffb887`79a2eaa8 00000000`00000000 : nt!NtDeviceIoControlFile+0x56
ffffb887`79a2ea90 00007ffe`1830be74 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
0000004e`66eff538 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffe`1830be74
SYMBOL_NAME: nsiproxy!NsippDispatch+b4
MODULE_NAME: nsiproxy
IMAGE_NAME: nsiproxy.sys
IMAGE_VERSION: 10.0.19041.1124
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: b4
FAILURE_BUCKET_ID: 0x44_nsiproxy!NsippDispatch
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {4fb9d960-49ca-744e-ae5b-568d82c21f53}
Followup: MachineOwner
---------
APC_INDEX_MISMATCH (1)
This is a kernel internal error. The most common reason to see this
bugcheck is when a filesystem or a driver has a mismatched number of
calls to disable and re-enable APCs. The key data item is the
Thread->CombinedApcDisable field. This consists of two separate 16-bit
fields, the SpecialApcDisable and the KernelApcDisable. A negative value
of either indicates that a driver has disabled special or normal APCs
(respectively) without re-enabling them; a positive value indicates that
a driver has enabled special or normal APCs (respectively) too many times.
Arguments:
Arg1: 00007ff83b0abe14, Address of system call function or worker routine
Arg2: 0000000000000000, Thread->ApcStateIndex
Arg3: 000000000000ffff, (Thread->SpecialApcDisable << 16) | Thread->KernelApcDisable
Arg4: ffff900e0e995b80, Call type (0 - system call, 1 - worker routine)
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 3468
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-62N06FT
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 6354
Key : Analysis.Memory.CommitPeak.Mb
Value: 80
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 1
BUGCHECK_P1: 7ff83b0abe14
BUGCHECK_P2: 0
BUGCHECK_P3: ffff
BUGCHECK_P4: ffff900e0e995b80
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: EpicGamesLauncher.exe
STACK_TEXT:
ffff900e`0e9959b8 fffff803`5e006569 : 00000000`00000001 00007ff8`3b0abe14 00000000`00000000 00000000`0000ffff : nt!KeBugCheckEx
ffff900e`0e9959c0 fffff803`5e006433 : 00000000`00000000 ffffc501`574bc860 ffff900e`0e995b18 ffffffff`fffe7960 : nt!KiBugCheckDispatch+0x69
ffff900e`0e995b00 00007ff8`3b0abe14 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceExitPico+0x1fe
00000034`440cf918 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ff8`3b0abe14
SYMBOL_NAME: nt!KiSystemServiceExitPico+1fe
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.572
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 1fe
FAILURE_BUCKET_ID: 0x1_SysCallNum_4_nt!KiSystemServiceExitPico
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {52cd694c-15ec-48c3-924a-3539560711db}
Followup: MachineOwner
---------
SYSTEM_SERVICE_EXCEPTION (3b)
An exception happened while executing a system service routine.
Arguments:
Arg1: 00000000c0000005, Exception code that caused the bugcheck
Arg2: fffff8005aac1c9f, Address of the instruction which caused the bugcheck
Arg3: ffffaa89a08d0ee0, Address of the context record for the exception that caused the bugcheck
Arg4: 0000000000000000, zero.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4671
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-62N06FT
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 25018
Key : Analysis.Memory.CommitPeak.Mb
Value: 74
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 3b
BUGCHECK_P1: c0000005
BUGCHECK_P2: fffff8005aac1c9f
BUGCHECK_P3: ffffaa89a08d0ee0
BUGCHECK_P4: 0
CONTEXT: ffffaa89a08d0ee0 -- (.cxr 0xffffaa89a08d0ee0)
rax=ffffe78800000000 rbx=00000000889922c0 rcx=0000000000000001
rdx=0000000000000000 rsi=ffffe788115bcc60 rdi=ffffe7881193edc0
rip=fffff8005aac1c9f rsp=ffffaa89a08d18e0 rbp=ffffaa89a08d1b80
r8=0000000000000204 r9=000000000000000c r10=ffffe7880713beb0
r11=ffffd70712b2eb40 r12=0000000000000000 r13=0000000000000000
r14=ffffe788115bcd78 r15=0000000000000001
iopl=0 nv up ei pl nz na pe nc
cs=0010 ss=0018 ds=002b es=002b fs=0053 gs=002b efl=00050202
nt!IopXxxControlFile+0x48f:
fffff800`5aac1c9f 8b4030 mov eax,dword ptr [rax+30h] ds:002b:ffffe788`00000030=????????
Resetting default scope
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: Dragon.exe
STACK_TEXT:
ffffaa89`a08d18e0 fffff800`5aac17f6 : 00000000`00000001 00000000`00000614 00000000`00000000 00000223`1aeb27e8 : nt!IopXxxControlFile+0x48f
ffffaa89`a08d1a20 fffff800`5a805fb8 : 00000000`00000000 000000a4`df23f118 ffffaa89`00000000 ffffe788`127262e0 : nt!NtDeviceIoControlFile+0x56
ffffaa89`a08d1a90 00007ffc`18e8be74 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
000000a4`df23f628 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffc`18e8be74
SYMBOL_NAME: nt!IopXxxControlFile+48f
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.572
STACK_COMMAND: .cxr 0xffffaa89a08d0ee0 ; kb
BUCKET_ID_FUNC_OFFSET: 48f
FAILURE_BUCKET_ID: 0x3B_c0000005_nt!IopXxxControlFile
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {657bb511-7f5c-7ddc-acd3-e126b6d359c8}
Followup: MachineOwner
---------Sistem bilgilerinizi göremiyorum. Sistem özellikleriniz nedir?
ygtrcys
Decapat
- Katılım
- 24 Ekim 2020
- Mesajlar
- 57
Daha fazla
- Cinsiyet
- Erkek
B450M S2H.
Ryzen5 3600.
Corsair ventage 3000MHz 2X.
SanDisk Ultra 3D 500GB.
Palit GTX1660 Super.
Corsair Carbide Spec 05 650W PSU.
Coller Master masterfan MF120 3X.
Memtest86 uzun sürdügünden paylaşamıyorum önerdiğiniz testleri yapıp dönüş yapacağım.
Memtest86 ve HD Tune testini yaptım hiç hata bulmadı sürücülerin hepsini parçaların kendi sitesinden en gücelini indip kurdum HDD sentinelin ekran görüntüsüde böyle.
Ryzen5 3600.
Corsair ventage 3000MHz 2X.
SanDisk Ultra 3D 500GB.
Palit GTX1660 Super.
Corsair Carbide Spec 05 650W PSU.
Coller Master masterfan MF120 3X.
Memtest86 uzun sürdügünden paylaşamıyorum önerdiğiniz testleri yapıp dönüş yapacağım.
Memtest86 ve HD Tune testini yaptım hiç hata bulmadı sürücülerin hepsini parçaların kendi sitesinden en gücelini indip kurdum HDD sentinelin ekran görüntüsüde böyle.
Dosya Ekleri
Son düzenleme:
ygtrcys
Decapat
- Katılım
- 24 Ekim 2020
- Mesajlar
- 57
Daha fazla
- Cinsiyet
- Erkek
B450M S2H.
Ryzen5 3600.
Corsair ventage 3000MHz 2X.
SanDisk Ultra 3D 500GB.
Palit GTX1660 Super.
Corsair Carbide Spec 05 650W PSU.
Sistemi yeni topladım, BIOS'u güncelledim, Windows'u Windows'un kendi resmi internet sitesinden indirdim, sürücüleri resmi sitelerden en son sürümlerini kurdum; Memtest86, Heavyload, HDD Sentinel, HD Tune test programlarında test ettim, hiçbirinden bir hata mesajı almadım. 2 gündür uğraşıyorum, problemin kaynağını bulamadım.



Ryzen5 3600.
Corsair ventage 3000MHz 2X.
SanDisk Ultra 3D 500GB.
Palit GTX1660 Super.
Corsair Carbide Spec 05 650W PSU.
Sistemi yeni topladım, BIOS'u güncelledim, Windows'u Windows'un kendi resmi internet sitesinden indirdim, sürücüleri resmi sitelerden en son sürümlerini kurdum; Memtest86, Heavyload, HDD Sentinel, HD Tune test programlarında test ettim, hiçbirinden bir hata mesajı almadım. 2 gündür uğraşıyorum, problemin kaynağını bulamadım.



Daha fazla
- Sistem Özellikleri
- i5-12400F, RTX 3070
- Cinsiyet
- Erkek
- Meslek
- Bilgisayar Mühendisliği öğrencisi
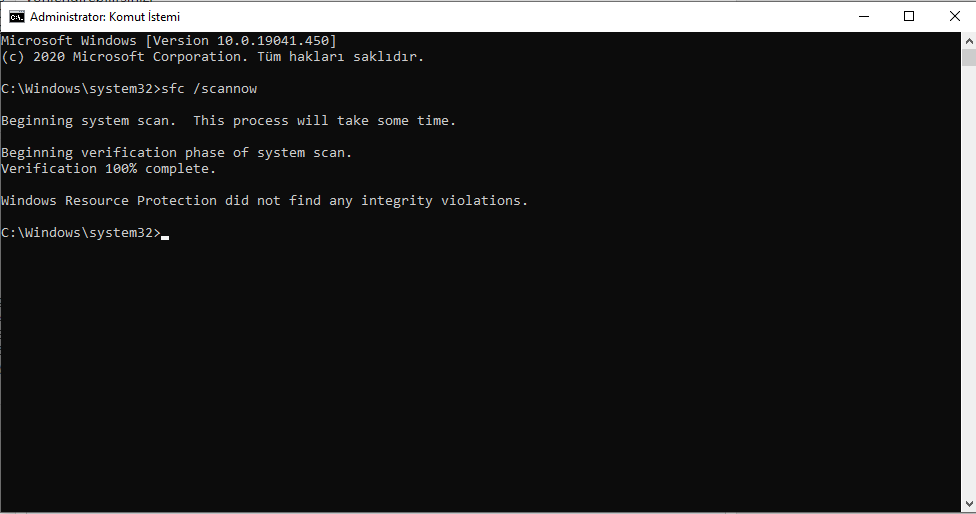
1) Aşağıdaki rehberi uygulayın ve sonuçları paylaşın.
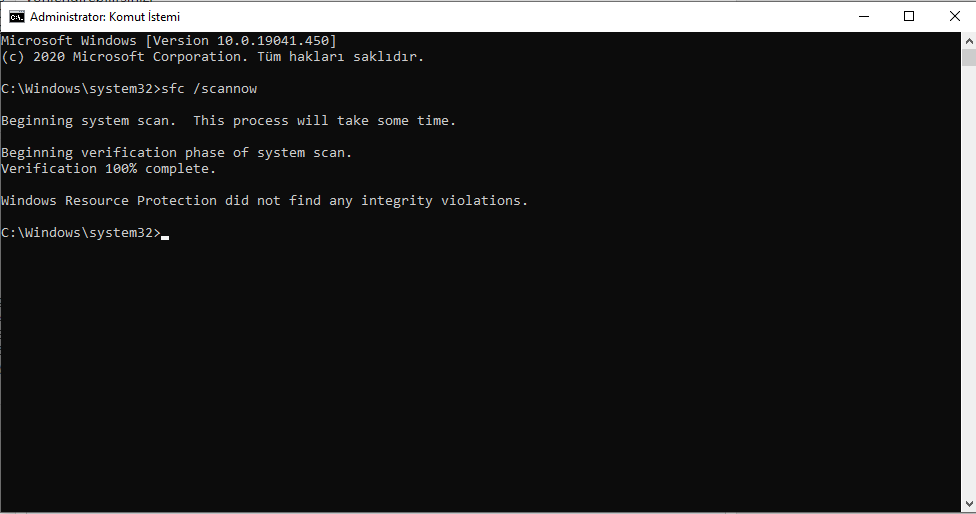
2) İnternetten DDU yazılımını ve aşağıdaki driverı indirin. Hepsi indirilince DDU'dan ses kartını seçip onun altından da Realtek (WIP) seçeceksiniz. Daha sonra işlemi başlatacaksınız. Bilgisayar kapandıktan sonra bilgisayarın internet bağlantısını kesip bu size verdiğim linkteki driverı kuracaksınız.
2) İnternetten DDU yazılımını ve aşağıdaki driverı indirin. Hepsi indirilince DDU'dan ses kartını seçip onun altından da Realtek (WIP) seçeceksiniz. Daha sonra işlemi başlatacaksınız. Bilgisayar kapandıktan sonra bilgisayarın internet bağlantısını kesip bu size verdiğim linkteki driverı kuracaksınız.
Son düzenleme:
- Katılım
- 28 Eylül 2016
- Mesajlar
- 10.910
- Makaleler
- 33
- Çözümler
- 293
Realtek LAN Driver sürücüsünü kaldırıp şu sürücüyü kurmayı dener misiniz?
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DPC_WATCHDOG_VIOLATION (133)
The DPC watchdog detected a prolonged run time at an IRQL of DISPATCH_LEVEL
or above.
Arguments:
Arg1: 0000000000000000, A single DPC or ISR exceeded its time allotment. The offending
component can usually be identified with a stack trace.
Arg2: 0000000000000501, The DPC time count (in ticks).
Arg3: 0000000000000500, The DPC time allotment (in ticks).
Arg4: fffff8061eafb320, cast to nt!DPC_WATCHDOG_GLOBAL_TRIAGE_BLOCK, which contains
additional information regarding this single DPC timeout
Debugging Details:
------------------
*************************************************************************
*** ***
*** ***
*** Either you specified an unqualified symbol, or your debugger ***
*** doesn't have full symbol information. Unqualified symbol ***
*** resolution is turned off by default. Please either specify a ***
*** fully qualified symbol module!symbolname, or enable resolution ***
*** of unqualified symbols by typing ".symopt- 100". Note that ***
*** enabling unqualified symbol resolution with network symbol ***
*** server shares in the symbol path may cause the debugger to ***
*** appear to hang for long periods of time when an incorrect ***
*** symbol name is typed or the network symbol server is down. ***
*** ***
*** For some commands to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: TickPeriods ***
*** ***
*************************************************************************
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 6515
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 16074
Key : Analysis.Memory.CommitPeak.Mb
Value: 82
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 133
BUGCHECK_P1: 0
BUGCHECK_P2: 501
BUGCHECK_P3: 500
BUGCHECK_P4: fffff8061eafb320
DPC_TIMEOUT_TYPE: SINGLE_DPC_TIMEOUT_EXCEEDED
TRAP_FRAME: ffff81825e629630 -- (.trap 0xffff81825e629630)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=000000003b587c49 rbx=0000000000000000 rcx=ffff81825e629820
rdx=ffff81825e629840 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8061e0bee17 rsp=ffff81825e6297c0 rbp=ffff81825e629960
r8=ffffa2816caa1280 r9=0000000000000000 r10=0000fffff8061e7a
r11=ffff927cd1400000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
nt!KeYieldProcessorEx+0x17:
fffff806`1e0bee17 4883c420 add rsp,20h
Resetting default scope
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
STACK_TEXT:
ffffa281`6cabae18 fffff806`1e287a14 : 00000000`00000133 00000000`00000000 00000000`00000501 00000000`00000500 : nt!KeBugCheckEx
ffffa281`6cabae20 fffff806`1e126993 : 00000d88`7de8e1c7 ffffa281`6caa1180 00000000`00000000 ffffa281`6caa1180 : nt!KeAccumulateTicks+0x15dd24
ffffa281`6cabae80 fffff806`1e12647a : ffffd588`ac2c5480 ffff8182`5e6296b0 ffff8182`5e629b00 00000000`00000000 : nt!KeClockInterruptNotify+0x453
ffffa281`6cabaf30 fffff806`1e02ecd5 : ffffd588`ac2c5480 00000000`00000000 00000000`00000000 ffff75f3`b7beef5d : nt!HalpTimerClockIpiRoutine+0x1a
ffffa281`6cabaf60 fffff806`1e1f604a : ffff8182`5e6296b0 ffffd588`ac2c5480 00000d77`c0584f13 00000000`00000000 : nt!KiCallInterruptServiceRoutine+0xa5
ffffa281`6cabafb0 fffff806`1e1f65b7 : 00000009`92feeda6 fffff806`219c96af ffff8182`5e629840 fffff806`1e1f65c4 : nt!KiInterruptSubDispatchNoLockNoEtw+0xfa
ffff8182`5e629630 fffff806`1e0bee17 : 00000000`00000010 00000000`00000282 ffff8182`5e6297e8 00000000`00000018 : nt!KiInterruptDispatchNoLockNoEtw+0x37
ffff8182`5e6297c0 fffff806`1e7a9719 : 00000000`00000002 00000000`00000000 ffffa281`6caa1180 00000000`00000001 : nt!KeYieldProcessorEx+0x17
ffff8182`5e6297f0 fffff806`1e7a7ff5 : 00000000`3b587c49 ffffa281`6caa1180 ffffd588`b132a5d0 00000000`00000000 : nt!IopLiveDumpProcessCorralStateChange+0x2d
ffff8182`5e629820 fffff806`1e0e549e : ffffa281`6caa4240 00000000`00000000 00000000`00000000 00000000`00000000 : nt!IopLiveDumpCorralDpc+0x55
ffff8182`5e629860 fffff806`1e0e4784 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x30e
ffff8182`5e6299d0 fffff806`1e1f810e : ffffffff`00000000 ffffa281`6caa1180 ffffa281`6caac340 ffffd588`b76ba040 : nt!KiRetireDpcList+0x1f4
ffff8182`5e629c60 00000000`00000000 : ffff8182`5e62a000 ffff8182`5e624000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KeAccumulateTicks+15dd24
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.572
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 15dd24
FAILURE_BUCKET_ID: 0x133_DPC_nt!KeAccumulateTicks
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {88dc98ce-f842-4daa-98d0-858621db6b0f}
Followup: MachineOwner
---------
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DPC_WATCHDOG_VIOLATION (133)
The DPC watchdog detected a prolonged run time at an IRQL of DISPATCH_LEVEL
or above.
Arguments:
Arg1: 0000000000000000, A single DPC or ISR exceeded its time allotment. The offending
component can usually be identified with a stack trace.
Arg2: 0000000000000501, The DPC time count (in ticks).
Arg3: 0000000000000500, The DPC time allotment (in ticks).
Arg4: fffff8061eafb320, cast to nt!DPC_WATCHDOG_GLOBAL_TRIAGE_BLOCK, which contains
additional information regarding this single DPC timeout
Debugging Details:
------------------
*************************************************************************
*** ***
*** ***
*** Either you specified an unqualified symbol, or your debugger ***
*** doesn't have full symbol information. Unqualified symbol ***
*** resolution is turned off by default. Please either specify a ***
*** fully qualified symbol module!symbolname, or enable resolution ***
*** of unqualified symbols by typing ".symopt- 100". Note that ***
*** enabling unqualified symbol resolution with network symbol ***
*** server shares in the symbol path may cause the debugger to ***
*** appear to hang for long periods of time when an incorrect ***
*** symbol name is typed or the network symbol server is down. ***
*** ***
*** For some commands to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: TickPeriods ***
*** ***
*************************************************************************
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 6515
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 16074
Key : Analysis.Memory.CommitPeak.Mb
Value: 82
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 133
BUGCHECK_P1: 0
BUGCHECK_P2: 501
BUGCHECK_P3: 500
BUGCHECK_P4: fffff8061eafb320
DPC_TIMEOUT_TYPE: SINGLE_DPC_TIMEOUT_EXCEEDED
TRAP_FRAME: ffff81825e629630 -- (.trap 0xffff81825e629630)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=000000003b587c49 rbx=0000000000000000 rcx=ffff81825e629820
rdx=ffff81825e629840 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8061e0bee17 rsp=ffff81825e6297c0 rbp=ffff81825e629960
r8=ffffa2816caa1280 r9=0000000000000000 r10=0000fffff8061e7a
r11=ffff927cd1400000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
nt!KeYieldProcessorEx+0x17:
fffff806`1e0bee17 4883c420 add rsp,20h
Resetting default scope
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
STACK_TEXT:
ffffa281`6cabae18 fffff806`1e287a14 : 00000000`00000133 00000000`00000000 00000000`00000501 00000000`00000500 : nt!KeBugCheckEx
ffffa281`6cabae20 fffff806`1e126993 : 00000d88`7de8e1c7 ffffa281`6caa1180 00000000`00000000 ffffa281`6caa1180 : nt!KeAccumulateTicks+0x15dd24
ffffa281`6cabae80 fffff806`1e12647a : ffffd588`ac2c5480 ffff8182`5e6296b0 ffff8182`5e629b00 00000000`00000000 : nt!KeClockInterruptNotify+0x453
ffffa281`6cabaf30 fffff806`1e02ecd5 : ffffd588`ac2c5480 00000000`00000000 00000000`00000000 ffff75f3`b7beef5d : nt!HalpTimerClockIpiRoutine+0x1a
ffffa281`6cabaf60 fffff806`1e1f604a : ffff8182`5e6296b0 ffffd588`ac2c5480 00000d77`c0584f13 00000000`00000000 : nt!KiCallInterruptServiceRoutine+0xa5
ffffa281`6cabafb0 fffff806`1e1f65b7 : 00000009`92feeda6 fffff806`219c96af ffff8182`5e629840 fffff806`1e1f65c4 : nt!KiInterruptSubDispatchNoLockNoEtw+0xfa
ffff8182`5e629630 fffff806`1e0bee17 : 00000000`00000010 00000000`00000282 ffff8182`5e6297e8 00000000`00000018 : nt!KiInterruptDispatchNoLockNoEtw+0x37
ffff8182`5e6297c0 fffff806`1e7a9719 : 00000000`00000002 00000000`00000000 ffffa281`6caa1180 00000000`00000001 : nt!KeYieldProcessorEx+0x17
ffff8182`5e6297f0 fffff806`1e7a7ff5 : 00000000`3b587c49 ffffa281`6caa1180 ffffd588`b132a5d0 00000000`00000000 : nt!IopLiveDumpProcessCorralStateChange+0x2d
ffff8182`5e629820 fffff806`1e0e549e : ffffa281`6caa4240 00000000`00000000 00000000`00000000 00000000`00000000 : nt!IopLiveDumpCorralDpc+0x55
ffff8182`5e629860 fffff806`1e0e4784 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x30e
ffff8182`5e6299d0 fffff806`1e1f810e : ffffffff`00000000 ffffa281`6caa1180 ffffa281`6caac340 ffffd588`b76ba040 : nt!KiRetireDpcList+0x1f4
ffff8182`5e629c60 00000000`00000000 : ffff8182`5e62a000 ffff8182`5e624000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KeAccumulateTicks+15dd24
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.572
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 15dd24
FAILURE_BUCKET_ID: 0x133_DPC_nt!KeAccumulateTicks
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {88dc98ce-f842-4daa-98d0-858621db6b0f}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DRIVER_IRQL_NOT_LESS_OR_EQUAL (d1)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If kernel debugger is available get stack backtrace.
Arguments:
Arg1: 0000000000000001, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000000, value 0 = read operation, 1 = write operation
Arg4: fffff80237b12cf0, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 7468
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 12002
Key : Analysis.Memory.CommitPeak.Mb
Value: 92
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: d1
BUGCHECK_P1: 1
BUGCHECK_P2: 2
BUGCHECK_P3: 0
BUGCHECK_P4: fffff80237b12cf0
READ_ADDRESS: fffff802338fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8023380f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8023380f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000001
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8023846a710 -- (.trap 0xfffff8023846a710)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000003 rbx=0000000000000000 rcx=edd8cdc527ac0000
rdx=0000000000000120 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80237b12cf0 rsp=fffff8023846a8a0 rbp=ffffc8837017c8e0
r8=0000000000000001 r9=fffff80238469900 r10=0000fffff80237ac
r11=ffff74ffb8a00000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
tcpip!TcpReceive+0x460:
fffff802`37b12cf0 4c8b37 mov r14,qword ptr [rdi] ds:00000000`00000000=????????????????
Resetting default scope
STACK_TEXT:
fffff802`3846a5c8 fffff802`33005e69 : 00000000`0000000a 00000000`00000001 00000000`00000002 00000000`00000000 : nt!KeBugCheckEx
fffff802`3846a5d0 fffff802`33002169 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiBugCheckDispatch+0x69
fffff802`3846a710 fffff802`37b12cf0 : ffffc883`73a55010 00000000`00000000 00000000`2e0dca4c fffff802`37caa598 : nt!KiPageFault+0x469
fffff802`3846a8a0 fffff802`37abe392 : ffffc883`6ceebb00 00000000`00005000 00000000`00000000 ffffc883`701ec001 : tcpip!TcpReceive+0x460
fffff802`3846a990 fffff802`37b0e540 : ffffc883`7061c030 fffff802`32ed1f35 00000000`00000000 ffffc883`6c7fa240 : tcpip!TcpNlClientReceiveDatagrams+0x22
fffff802`3846a9d0 fffff802`37b0ec7b : 00000000`00000001 00000000`00000000 00000000`00000000 ffffc883`701ec000 : tcpip!IppProcessDeliverList+0xc0
fffff802`3846aab0 fffff802`37b0b2ff : fffff802`37caa230 ffffc883`701528a0 ffffc883`701ec000 00000000`00000000 : tcpip!IppReceiveHeaderBatch+0x21b
fffff802`3846abb0 fffff802`37b0afbc : ffffc883`720f27c0 ffffc883`7061c030 00000000`00000001 00000000`00000000 : tcpip!IppFlcReceivePacketsCore+0x32f
fffff802`3846acd0 fffff802`37b2a47f : ffffc883`7061c030 00000000`00000000 fffff802`3846ada1 00000000`00000000 : tcpip!IpFlcReceivePackets+0xc
fffff802`3846ad00 fffff802`37b29a7c : 00000000`00000001 ffffc883`707e6000 fffff802`37ab3780 fffff802`3846b0dc : tcpip!FlpReceiveNonPreValidatedNetBufferListChain+0x26f
fffff802`3846ae00 fffff802`32eb8908 : ffffc883`7026a120 00000000`00000002 fffff802`33926600 fffff802`3846b0f8 : tcpip!FlReceiveNetBufferListChainCalloutRoutine+0x17c
fffff802`3846af50 fffff802`32eb887d : fffff802`37b29900 fffff802`3846b0f8 ffffc883`6cf5bef0 fffff802`37c73144 : nt!KeExpandKernelStackAndCalloutInternal+0x78
fffff802`3846afc0 fffff802`37ab331d : 00000000`00000014 fffff802`37b46b54 ffffc883`7061c1b0 fffff802`37da142f : nt!KeExpandKernelStackAndCalloutEx+0x1d
fffff802`3846b000 fffff802`37ab29fd : 00000000`00000001 fffff802`3846b160 ffffc883`707e6010 fffff802`3846b170 : tcpip!NetioExpandKernelStackAndCallout+0x8d
fffff802`3846b060 fffff802`37861eb0 : ffffc883`706f6ae1 00000000`00000001 ffffc883`70316070 fffff802`3846b470 : tcpip!FlReceiveNetBufferListChain+0x46d
fffff802`3846b310 fffff802`37861ccb : ffffc883`707e8690 fffff802`00000001 fffff802`00000000 00000000`00000001 : ndis!ndisMIndicateNetBufferListsToOpen+0x140
fffff802`3846b3f0 fffff802`37867ef0 : ffffc883`704601a0 ffffc883`7061c001 ffffc883`704601a0 00000000`00000001 : ndis!ndisMTopReceiveNetBufferLists+0x22b
fffff802`3846b470 fffff802`3789dcf3 : ffffc883`7061c030 fffff802`3846b541 00000000`00000000 00000000`00000000 : ndis!ndisCallReceiveHandler+0x60
fffff802`3846b4c0 fffff802`37864a94 : 00000000`00004b95 00000000`00000001 ffffc883`704601a0 00000000`00000001 : ndis!ndisInvokeNextReceiveHandler+0x1df
fffff802`3846b590 fffff802`412161d8 : ffffc883`70503000 ffffc883`70503000 00000000`00000000 ffffc883`705035f0 : ndis!NdisMIndicateReceiveNetBufferLists+0x104
fffff802`3846b620 fffff802`412025a8 : 00000000`00000000 fffff802`32f07c01 00000107`00000400 fffff802`3846b798 : rt640x64!MpHandleRecvIntPriVLanJumbo+0x2c4
fffff802`3846b710 fffff802`37867886 : 00000000`ffffffff ffffc883`70645280 ffffc883`70674108 00000000`00000000 : rt640x64!MPHandleMessageInterrupt+0x398
fffff802`3846b780 fffff802`32ee9a3e : fffff802`3083e240 00000000`00000000 00000000`00000001 00000000`00000000 : ndis!ndisInterruptDpc+0x196
fffff802`3846b860 fffff802`32ee8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x30e
fffff802`3846b9d0 fffff802`32ff7a0e : 00000000`00000000 fffff802`3083b180 fffff802`33926600 ffffc883`74a0a080 : nt!KiRetireDpcList+0x1f4
fffff802`3846bc60 00000000`00000000 : fffff802`3846c000 fffff802`38466000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: rt640x64!MpHandleRecvIntPriVLanJumbo+2c4
MODULE_NAME: rt640x64
IMAGE_NAME: rt640x64.sys
IMAGE_VERSION: 9.1.410.2015
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2c4
FAILURE_BUCKET_ID: AV_rt640x64!MpHandleRecvIntPriVLanJumbo
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {e85833a8-915f-a98a-61ce-bd85f0b49fd7}
Followup: MachineOwner
---------
* *
* Bugcheck Analysis *
* *
*******************************************************************************
DRIVER_IRQL_NOT_LESS_OR_EQUAL (d1)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If kernel debugger is available get stack backtrace.
Arguments:
Arg1: 0000000000000001, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000000, value 0 = read operation, 1 = write operation
Arg4: fffff80237b12cf0, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 7468
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 12002
Key : Analysis.Memory.CommitPeak.Mb
Value: 92
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: d1
BUGCHECK_P1: 1
BUGCHECK_P2: 2
BUGCHECK_P3: 0
BUGCHECK_P4: fffff80237b12cf0
READ_ADDRESS: fffff802338fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8023380f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8023380f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000001
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8023846a710 -- (.trap 0xfffff8023846a710)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000003 rbx=0000000000000000 rcx=edd8cdc527ac0000
rdx=0000000000000120 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80237b12cf0 rsp=fffff8023846a8a0 rbp=ffffc8837017c8e0
r8=0000000000000001 r9=fffff80238469900 r10=0000fffff80237ac
r11=ffff74ffb8a00000 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl nz na pe nc
tcpip!TcpReceive+0x460:
fffff802`37b12cf0 4c8b37 mov r14,qword ptr [rdi] ds:00000000`00000000=????????????????
Resetting default scope
STACK_TEXT:
fffff802`3846a5c8 fffff802`33005e69 : 00000000`0000000a 00000000`00000001 00000000`00000002 00000000`00000000 : nt!KeBugCheckEx
fffff802`3846a5d0 fffff802`33002169 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiBugCheckDispatch+0x69
fffff802`3846a710 fffff802`37b12cf0 : ffffc883`73a55010 00000000`00000000 00000000`2e0dca4c fffff802`37caa598 : nt!KiPageFault+0x469
fffff802`3846a8a0 fffff802`37abe392 : ffffc883`6ceebb00 00000000`00005000 00000000`00000000 ffffc883`701ec001 : tcpip!TcpReceive+0x460
fffff802`3846a990 fffff802`37b0e540 : ffffc883`7061c030 fffff802`32ed1f35 00000000`00000000 ffffc883`6c7fa240 : tcpip!TcpNlClientReceiveDatagrams+0x22
fffff802`3846a9d0 fffff802`37b0ec7b : 00000000`00000001 00000000`00000000 00000000`00000000 ffffc883`701ec000 : tcpip!IppProcessDeliverList+0xc0
fffff802`3846aab0 fffff802`37b0b2ff : fffff802`37caa230 ffffc883`701528a0 ffffc883`701ec000 00000000`00000000 : tcpip!IppReceiveHeaderBatch+0x21b
fffff802`3846abb0 fffff802`37b0afbc : ffffc883`720f27c0 ffffc883`7061c030 00000000`00000001 00000000`00000000 : tcpip!IppFlcReceivePacketsCore+0x32f
fffff802`3846acd0 fffff802`37b2a47f : ffffc883`7061c030 00000000`00000000 fffff802`3846ada1 00000000`00000000 : tcpip!IpFlcReceivePackets+0xc
fffff802`3846ad00 fffff802`37b29a7c : 00000000`00000001 ffffc883`707e6000 fffff802`37ab3780 fffff802`3846b0dc : tcpip!FlpReceiveNonPreValidatedNetBufferListChain+0x26f
fffff802`3846ae00 fffff802`32eb8908 : ffffc883`7026a120 00000000`00000002 fffff802`33926600 fffff802`3846b0f8 : tcpip!FlReceiveNetBufferListChainCalloutRoutine+0x17c
fffff802`3846af50 fffff802`32eb887d : fffff802`37b29900 fffff802`3846b0f8 ffffc883`6cf5bef0 fffff802`37c73144 : nt!KeExpandKernelStackAndCalloutInternal+0x78
fffff802`3846afc0 fffff802`37ab331d : 00000000`00000014 fffff802`37b46b54 ffffc883`7061c1b0 fffff802`37da142f : nt!KeExpandKernelStackAndCalloutEx+0x1d
fffff802`3846b000 fffff802`37ab29fd : 00000000`00000001 fffff802`3846b160 ffffc883`707e6010 fffff802`3846b170 : tcpip!NetioExpandKernelStackAndCallout+0x8d
fffff802`3846b060 fffff802`37861eb0 : ffffc883`706f6ae1 00000000`00000001 ffffc883`70316070 fffff802`3846b470 : tcpip!FlReceiveNetBufferListChain+0x46d
fffff802`3846b310 fffff802`37861ccb : ffffc883`707e8690 fffff802`00000001 fffff802`00000000 00000000`00000001 : ndis!ndisMIndicateNetBufferListsToOpen+0x140
fffff802`3846b3f0 fffff802`37867ef0 : ffffc883`704601a0 ffffc883`7061c001 ffffc883`704601a0 00000000`00000001 : ndis!ndisMTopReceiveNetBufferLists+0x22b
fffff802`3846b470 fffff802`3789dcf3 : ffffc883`7061c030 fffff802`3846b541 00000000`00000000 00000000`00000000 : ndis!ndisCallReceiveHandler+0x60
fffff802`3846b4c0 fffff802`37864a94 : 00000000`00004b95 00000000`00000001 ffffc883`704601a0 00000000`00000001 : ndis!ndisInvokeNextReceiveHandler+0x1df
fffff802`3846b590 fffff802`412161d8 : ffffc883`70503000 ffffc883`70503000 00000000`00000000 ffffc883`705035f0 : ndis!NdisMIndicateReceiveNetBufferLists+0x104
fffff802`3846b620 fffff802`412025a8 : 00000000`00000000 fffff802`32f07c01 00000107`00000400 fffff802`3846b798 : rt640x64!MpHandleRecvIntPriVLanJumbo+0x2c4
fffff802`3846b710 fffff802`37867886 : 00000000`ffffffff ffffc883`70645280 ffffc883`70674108 00000000`00000000 : rt640x64!MPHandleMessageInterrupt+0x398
fffff802`3846b780 fffff802`32ee9a3e : fffff802`3083e240 00000000`00000000 00000000`00000001 00000000`00000000 : ndis!ndisInterruptDpc+0x196
fffff802`3846b860 fffff802`32ee8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x30e
fffff802`3846b9d0 fffff802`32ff7a0e : 00000000`00000000 fffff802`3083b180 fffff802`33926600 ffffc883`74a0a080 : nt!KiRetireDpcList+0x1f4
fffff802`3846bc60 00000000`00000000 : fffff802`3846c000 fffff802`38466000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: rt640x64!MpHandleRecvIntPriVLanJumbo+2c4
MODULE_NAME: rt640x64
IMAGE_NAME: rt640x64.sys
IMAGE_VERSION: 9.1.410.2015
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2c4
FAILURE_BUCKET_ID: AV_rt640x64!MpHandleRecvIntPriVLanJumbo
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {e85833a8-915f-a98a-61ce-bd85f0b49fd7}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
REFERENCE_BY_POINTER (18)
Arguments:
Arg1: ffff9e8d0e4f4380, Object type of the object whose reference count is being lowered
Arg2: ffffc58bc07bd4f0, Object whose reference count is being lowered
Arg3: 0000000000000001, Reserved
Arg4: ffffffffffffffff, Reserved
The reference count of an object is illegal for the current state of the object.
Each time a driver uses a pointer to an object the driver calls a kernel routine
to increment the reference count of the object. When the driver is done with the
pointer the driver calls another kernel routine to decrement the reference count.
Drivers must match calls to the increment and decrement routines. This bugcheck
can occur because an object's reference count goes to zero while there are still
open handles to the object, in which case the fourth parameter indicates the number
of opened handles. It may also occur when the object's reference count drops below zero
whether or not there are open handles to the object, and in that case the fourth parameter
contains the actual value of the pointer references count.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4921
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 9984
Key : Analysis.Memory.CommitPeak.Mb
Value: 76
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 18
BUGCHECK_P1: ffff9e8d0e4f4380
BUGCHECK_P2: ffffc58bc07bd4f0
BUGCHECK_P3: 1
BUGCHECK_P4: ffffffffffffffff
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: svchost.exe
STACK_TEXT:
fffff081`78ddb908 fffff801`51a6ba1c : 00000000`00000018 ffff9e8d`0e4f4380 ffffc58b`c07bd4f0 00000000`00000001 : nt!KeBugCheckEx
fffff081`78ddb910 fffff801`51cd243e : ffff9e8d`0e4f4380 00000000`00000000 00000000`00000000 ffffc58b`b86b2f40 : nt!ObfDereferenceObjectWithTag+0x18bb1c
fffff081`78ddb950 fffff801`51cd60bc : 00000000`000003d0 00000000`00000000 00000000`00000000 00000000`00000000 : nt!ObCloseHandleTableEntry+0x29e
fffff081`78ddba90 fffff801`51a058b8 : ffff9e8d`1619e000 000000ce`ddfcda50 fffff081`78ddbb80 ffff9e8d`14e10a80 : nt!NtClose+0xec
fffff081`78ddbb00 00007ffa`03b8bfa4 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
000000ce`ddfcdf48 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffa`03b8bfa4
SYMBOL_NAME: nt!ObfDereferenceObjectWithTag+18bb1c
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 18bb1c
FAILURE_BUCKET_ID: 0x18_OVER_DEREFERENCE_nt!ObfDereferenceObjectWithTag
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {4139309c-4e9f-52f0-ac5e-4041e7a86a20}
Followup: MachineOwner
---------
* *
* Bugcheck Analysis *
* *
*******************************************************************************
REFERENCE_BY_POINTER (18)
Arguments:
Arg1: ffff9e8d0e4f4380, Object type of the object whose reference count is being lowered
Arg2: ffffc58bc07bd4f0, Object whose reference count is being lowered
Arg3: 0000000000000001, Reserved
Arg4: ffffffffffffffff, Reserved
The reference count of an object is illegal for the current state of the object.
Each time a driver uses a pointer to an object the driver calls a kernel routine
to increment the reference count of the object. When the driver is done with the
pointer the driver calls another kernel routine to decrement the reference count.
Drivers must match calls to the increment and decrement routines. This bugcheck
can occur because an object's reference count goes to zero while there are still
open handles to the object, in which case the fourth parameter indicates the number
of opened handles. It may also occur when the object's reference count drops below zero
whether or not there are open handles to the object, and in that case the fourth parameter
contains the actual value of the pointer references count.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4921
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on XYZ-PC
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 9984
Key : Analysis.Memory.CommitPeak.Mb
Value: 76
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 18
BUGCHECK_P1: ffff9e8d0e4f4380
BUGCHECK_P2: ffffc58bc07bd4f0
BUGCHECK_P3: 1
BUGCHECK_P4: ffffffffffffffff
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: svchost.exe
STACK_TEXT:
fffff081`78ddb908 fffff801`51a6ba1c : 00000000`00000018 ffff9e8d`0e4f4380 ffffc58b`c07bd4f0 00000000`00000001 : nt!KeBugCheckEx
fffff081`78ddb910 fffff801`51cd243e : ffff9e8d`0e4f4380 00000000`00000000 00000000`00000000 ffffc58b`b86b2f40 : nt!ObfDereferenceObjectWithTag+0x18bb1c
fffff081`78ddb950 fffff801`51cd60bc : 00000000`000003d0 00000000`00000000 00000000`00000000 00000000`00000000 : nt!ObCloseHandleTableEntry+0x29e
fffff081`78ddba90 fffff801`51a058b8 : ffff9e8d`1619e000 000000ce`ddfcda50 fffff081`78ddbb80 ffff9e8d`14e10a80 : nt!NtClose+0xec
fffff081`78ddbb00 00007ffa`03b8bfa4 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
000000ce`ddfcdf48 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffa`03b8bfa4
SYMBOL_NAME: nt!ObfDereferenceObjectWithTag+18bb1c
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 18bb1c
FAILURE_BUCKET_ID: 0x18_OVER_DEREFERENCE_nt!ObfDereferenceObjectWithTag
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {4139309c-4e9f-52f0-ac5e-4041e7a86a20}
Followup: MachineOwner
---------
Daha fazla
- Sistem Özellikleri
- i5-12400F, RTX 3070
- Cinsiyet
- Erkek
- Meslek
- Bilgisayar Mühendisliği öğrencisi
Tüm işlemleri uyguladıktan sonra tekrar alırsanız sadece yeni minidump dosyanızı paylaşırsınız. Yarına kadar ise tekrar hata almazsanız lütfen tekrar gelip sorununuzun çözüldüğünü belirtmeyi unutmayın.
ygtrcys
Decapat
- Katılım
- 24 Ekim 2020
- Mesajlar
- 57
Daha fazla
- Cinsiyet
- Erkek
Tüm işlemleri uyguladıktan sonra tekrar alırsanız sadece yeni minidump dosyanızı paylaşırsınız. Yarına kadar ise tekrar hata almazsanız lütfen tekrar gelip sorununuzun çözüldüğünü belirtmeyi unutmayın.
Öncelikle çok teşekkürler 2 gündür beyinimi yoran problemi çözdügün için. Sabaha kadar oyun oynadım ve mavi ekranla karşılaşmadım. Umarım konu aynı problemleri yaşayan arkadaşlar için rehber olur.
Tüm işlemleri uyguladıktan sonra tekrar alırsanız sadece yeni minidump dosyanızı paylaşırsınız. Yarına kadar ise tekrar hata almazsanız lütfen tekrar gelip sorununuzun çözüldüğünü belirtmeyi unutmayın.
Bir minidump daha

Son düzenleme:
Benzer konular
Yeni konular
-
-
-
-
-
-
HyperX Cloud 2 ses kartına asitli içecek döküldü
- ineffablefishy
- Mesaj: 20
-
-
-
-
-



