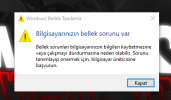
Selamlar, sanal belleği kapatın ve sistemi yeniden başlatın. Ardından sanal belleği tekrardan açın ve sistemi yeniden başlatın. Ayarı otomatiğe alabilirsiniz, bilginize. Gerekli rehber aşağıda yer almaktadır, 3-5 gün boyunca sistemi kullanıp sonuçları bizimle paylaşırsanız sevinirim.
[CODE title="Dökümler"]*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
MEMORY_MANAGEMENT (1a)
# Any other values for parameter 1 must be individually examined.
Arguments:
Arg1: 0000000000041792, A corrupt PTE has been detected. Parameter 2 contains the address of
the PTE. Parameters 3/4 contain the low/high parts of the PTE.
Arg2: ffffcc012069abb0
Arg3: 0000000010000000
Arg4: 0000000000000000
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 7780
Key : Analysis.DebugAnalysisManager
Value: Create
Key : Analysis.Elapsed.mSec
Value: 11122
Key : Analysis.Init.CPU.mSec
Value: 1078
Key : Analysis.Init.Elapsed.mSec
Value: 4988
Key : Analysis.Memory.CommitPeak.Mb
Value: 74
Key : MemoryManagement.PFN
Value: 10000
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
FILE_IN_CAB: 020322-13781-01.dmp
BUGCHECK_CODE: 1a
BUGCHECK_P1: 41792
BUGCHECK_P2: ffffcc012069abb0
BUGCHECK_P3: 10000000
BUGCHECK_P4: 0
MEMORY_CORRUPTOR: ONE_BIT
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: chrome.exe
STACK_TEXT:
ffff8884`9fc60f78 fffff800`3a8440ca : 00000000`0000001a 00000000`00041792 ffffcc01`2069abb0 00000000`10000000 : nt!KeBugCheckEx
ffff8884`9fc60f80 fffff800`3a89e556 : 00000000`00000000 00000000`00000000 00000000`00000025 ffffcc01`2069abb0 : nt!MiDeleteVa+0x153a
ffff8884`9fc61080 fffff800`3a89e66b : ffffcc66`00000000 ffffa60a`58924740 ffff8884`00000000 ffff8884`9fc614f0 : nt!MiWalkPageTablesRecursively+0x776
ffff8884`9fc61120 fffff800`3a89e66b : ffffcc66`33004818 ffffa60a`58924740 ffff8884`00000001 ffff8884`9fc61500 : nt!MiWalkPageTablesRecursively+0x88b
ffff8884`9fc611c0 fffff800`3a89e66b : ffffcc66`33004000 ffffa60a`58924740 ffff8884`00000002 ffff8884`9fc61510 : nt!MiWalkPageTablesRecursively+0x88b
ffff8884`9fc61260 fffff800`3a804f4b : 00000000`00000000 ffffa60a`58924740 00000000`00000003 ffff8884`9fc61520 : nt!MiWalkPageTablesRecursively+0x88b
ffff8884`9fc61300 fffff800`3a842961 : ffff8884`9fc614a0 ffffa60a`00000000 00000000`00000002 00000000`00000000 : nt!MiWalkPageTables+0x36b
ffff8884`9fc61400 fffff800`3a812aa0 : 00000000`00000001 ffff8884`00000000 ffffa60a`58924590 ffffa60a`57831080 : nt!MiDeletePagablePteRange+0x4f1
ffff8884`9fc61710 fffff800`3ac01149 : ffffa60a`586b4860 00000000`00000000 ffffa60a`00000000 ffffa60a`00000000 : nt!MiDeleteVad+0x360
ffff8884`9fc61820 fffff800`3ac007e0 : ffffa60a`586b4860 ffffa60a`58924d60 ffffa60a`57831080 00000000`00000000 : nt!MiUnmapVad+0x49
ffff8884`9fc61850 fffff800`3abfeaaf : ffffa60a`586b54e0 ffffa60a`586b54e0 ffffa60a`586b4860 ffffa60a`589240c0 : nt!MiCleanVad+0x30
ffff8884`9fc61880 fffff800`3ac5c5a8 : ffffffff`00000000 ffffffff`ffffffff 00000000`00000001 ffffa60a`589240c0 : nt!MmCleanProcessAddressSpace+0x137
ffff8884`9fc61900 fffff800`3acb0fe6 : ffffa60a`589240c0 ffffb78d`b040f770 00000000`00000000 00000000`00000000 : nt!PspRundownSingleProcess+0x20c
ffff8884`9fc61990 fffff800`3acb454e : ffffa60a`00000000 00000000`00000001 00000000`00000000 000000b3`9bc27000 : nt!PspExitThread+0x5f6
ffff8884`9fc61a90 fffff800`3aa08cb8 : ffffa60a`589240c0 ffffa60a`57831080 ffff8884`9fc61b80 ffffa60a`589240c0 : nt!NtTerminateProcess+0xde
ffff8884`9fc61b00 00007ffc`eff4d2f4 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
000000b3`9c5ffa88 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffc`eff4d2f4
MODULE_NAME: hardware
IMAGE_NAME: memory_corruption
STACK_COMMAND: .cxr; .ecxr ; kb
FAILURE_BUCKET_ID: MEMORY_CORRUPTION_ONE_BIT
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {e3faf315-c3d0-81db-819a-6c43d23c63a7}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
KMODE_EXCEPTION_NOT_HANDLED (1e)
This is a very common BugCheck. Usually the exception address pinpoints
the driver/function that caused the problem. Always note this address
as well as the link date of the driver/image that contains this address.
Arguments:
Arg1: ffffffffc0000005, The exception code that was not handled
Arg2: fffff8044314011a, The address that the exception occurred at
Arg3: 0000000000000000, Parameter 0 of the exception
Arg4: 000000010001b52d, Parameter 1 of the exception
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 8968
Key : Analysis.DebugAnalysisManager
Value: Create
Key : Analysis.Elapsed.mSec
Value: 27906
Key : Analysis.Init.CPU.mSec
Value: 1015
Key : Analysis.Init.Elapsed.mSec
Value: 5012
Key : Analysis.Memory.CommitPeak.Mb
Value: 77
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
FILE_IN_CAB: 020322-13703-01.dmp
BUGCHECK_CODE: 1e
BUGCHECK_P1: ffffffffc0000005
BUGCHECK_P2: fffff8044314011a
BUGCHECK_P3: 0
BUGCHECK_P4: 10001b52d
READ_ADDRESS: fffff804408fb390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
unable to get nt!MmSpecialPagesInUse
000000010001b52d
EXCEPTION_PARAMETER2: 000000010001b52d
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: RuntimeBroker.exe
TRAP_FRAME: ffff800000000000 -- (.trap 0xffff800000000000)
Unable to read trap frame at ffff8000`00000000
STACK_TEXT:
ffffac8f`ddae5be8 fffff804`40059fcb : 00000000`0000001e ffffffff`c0000005 fffff804`4314011a 00000000`00000000 : nt!KeBugCheckEx
ffffac8f`ddae5bf0 fffff804`400093ac : 00000000`00001000 ffffac8f`ddae6490 ffff8000`00000000 00000000`00000000 : nt!KiDispatchException+0x17463b
ffffac8f`ddae62b0 fffff804`40005543 : 00000000`00000000 00000000`00000000 00000000`00000000 fffff804`401f3cfb : nt!KiExceptionDispatch+0x12c
ffffac8f`ddae6490 fffff804`4314011a : ffff8a09`54ce5a88 ffff9a85`83847660 ffff8a09`540e74e0 ffff9a85`83847b78 : nt!KiPageFault+0x443
ffffac8f`ddae6620 fffff804`4313d52a : ffff8a09`522eacc8 ffff8a09`54ce5a88 ffff8a09`46d4e180 ffff9a85`83847b78 : Ntfs!NtfsOpenAttribute+0xdfa
ffffac8f`ddae67c0 fffff804`4313ca44 : 00000000`00000000 ffffac8f`def1ce00 ffffac8f`def1d0e0 fffff804`00000066 : Ntfs!NtfsOpenExistingAttr+0x1fa
ffffac8f`ddae6880 fffff804`4313baaa : ffffac8f`def1d0e0 ffff9a85`83848200 ffff9a85`83847660 ffff9a85`83847660 : Ntfs!NtfsOpenAttributeInExistingFile+0x494
ffffac8f`ddae6a70 fffff804`430e921f : ffff8a09`522eacc8 ffff8a09`46d4f4f0 ffff9a85`79677810 00000000`00000001 : Ntfs!NtfsOpenExistingPrefixFcb+0x22a
ffffac8f`ddae6b80 fffff804`430ea120 : ffff8a09`522eacc8 ffff8a09`54ce5730 ffff8a09`522eacc8 ffffac8f`ddae6e20 : Ntfs!NtfsFindStartingNode+0x3ff
ffffac8f`ddae6c70 fffff804`4314d9b2 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : Ntfs!NtfsCommonCreate+0x580
ffffac8f`ddae6f50 fffff804`3fffabbe : ffffac8f`def1cf90 ffffac8f`ddae6fd0 00000000`00000000 00000000`00000001 : Ntfs!NtfsCommonCreateCallout+0x22
ffffac8f`ddae6f80 fffff804`3fffab7c : ffffac8f`ddae6fd0 ffff8a09`5157d080 ffffac8f`ddae7000 fffff804`3fef88fd : nt!KxSwitchKernelStackCallout+0x2e
ffffac8f`def1cd80 fffff804`3fef88fd : ffffac8f`ddae6fd0 ffff8a09`5157d080 ffffac8f`def1ce00 00000000`00000001 : nt!KiSwitchKernelStackContinue
ffffac8f`def1cda0 fffff804`3fef86f2 : fffff804`4314d990 ffffac8f`def1cf90 00000000`00000002 00000000`00000000 : nt!KiExpandKernelStackAndCalloutOnStackSegment+0x19d
ffffac8f`def1ce40 fffff804`3fef8553 : 00000000`00000008 ffffac8f`def1d0e0 00000000`00000000 ffff8a09`54ce5730 : nt!KiExpandKernelStackAndCalloutSwitchStack+0xf2
ffffac8f`def1ceb0 fffff804`3fef850d : fffff804`4314d990 ffffac8f`def1cf90 ffff8a09`54ce5730 ffffac8f`def19000 : nt!KeExpandKernelStackAndCalloutInternal+0x33
ffffac8f`def1cf20 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KeExpandKernelStackAndCalloutEx+0x1d
SYMBOL_NAME: Ntfs!NtfsOpenAttribute+dfa
MODULE_NAME: Ntfs
IMAGE_NAME: Ntfs.sys
IMAGE_VERSION: 10.0.19041.1173
STACK_COMMAND: .cxr; .ecxr ; kb
BUCKET_ID_FUNC_OFFSET: dfa
FAILURE_BUCKET_ID: 0x1E_c0000005_R_Ntfs!NtfsOpenAttribute
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {c0a976f8-a537-9453-c9b8-7544756edc5e}
Followup: MachineOwner
---------[/CODE]