*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
SYSTEM_SERVICE_EXCEPTION (3b)
An exception happened while executing a system service routine.
Arguments:
Arg1: 00000000c0000005, Exception code that caused the bugcheck
Arg2: fffff80576fdc59c, Address of the instruction which caused the bugcheck
Arg3: ffffd98a36e4bdd0, Address of the context record for the exception that caused the bugcheck
Arg4: 0000000000000000, zero.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
PROCESSES_ANALYSIS: 1
SERVICE_ANALYSIS: 1
STACKHASH_ANALYSIS: 1
TIMELINE_ANALYSIS: 1
DUMP_CLASS: 1
DUMP_QUALIFIER: 400
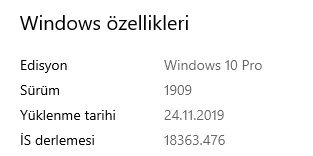
BUILD_VERSION_STRING: 10.0.18362.476 (WinBuild.160101.0800)
SYSTEM_MANUFACTURER: Micro-Star International Co., Ltd
SYSTEM_PRODUCT_NAME: MS-7C02
SYSTEM_SKU: To be filled by O.E.M.
SYSTEM_VERSION: 1.0
BIOS_VENDOR: American Megatrends Inc.
BIOS_VERSION: 3.40
BIOS_DATE: 10/25/2019
BASEBOARD_MANUFACTURER: Micro-Star International Co., Ltd
BASEBOARD_PRODUCT: B450 TOMAHAWK MAX (MS-7C02)
BASEBOARD_VERSION: 1.0
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
DUMP_TYPE: 2
BUGCHECK_P1: c0000005
BUGCHECK_P2: fffff80576fdc59c
BUGCHECK_P3: ffffd98a36e4bdd0
BUGCHECK_P4: 0
EXCEPTION_CODE: (NTSTATUS) 0xc0000005 - <Unable to get error code text>
FAULTING_IP:
nt!ObInsertObjectEx+cc
fffff805`76fdc59c f6474208 test byte ptr [rdi+42h],8
CONTEXT: ffffd98a36e4bdd0 -- (.cxr 0xffffd98a36e4bdd0)
rax=ffffc98b2f171080 rbx=ffffc98b301655a0 rcx=0000000000000000
rdx=0000000000000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80576fdc59c rsp=ffffd98a36e4c7c0 rbp=ffffd98a36e4c8c0
r8=0000000000000000 r9=fffff80576a00000 r10=0000000000000000
r11=ffffd98a36e4ca50 r12=ffffc98b2b6ff7c0 r13=ffffc98b2b6ff7f0
r14=000002bab3f80ba0 r15=ffffd98a36e4cac8
iopl=0 nv up ei pl zr na po nc
cs=0010 ss=0018 ds=002b es=002b fs=0053 gs=002b efl=00050246
nt!ObInsertObjectEx+0xcc:
fffff805`76fdc59c f6474208 test byte ptr [rdi+42h],8 ds:002b:00000000`00000042=??
Resetting default scope
BUGCHECK_STR: 0x3B_c0000005
CPU_COUNT: c
CPU_MHZ: e10
CPU_VENDOR: AuthenticAMD
CPU_FAMILY: 17
CPU_MODEL: 71
CPU_STEPPING: 0
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: WIN8_DRIVER_FAULT
PROCESS_NAME: chrome.exe
CURRENT_IRQL: 0
ANALYSIS_SESSION_HOST: DESKTOP-18V31A3
ANALYSIS_SESSION_TIME: 12-01-2019 13:12:44.0491
ANALYSIS_VERSION: 10.0.18362.1 x86fre
LAST_CONTROL_TRANSFER: from fffff805770bc05f to fffff80576fdc59c
STACK_TEXT:
ffffd98a`36e4c7c0 fffff805`770bc05f : 000002ba`b3f80ba0 ffffd98a`36e4cb80 00000000`00000001 000002ba`b3f80ba0 : nt!ObInsertObjectEx+0xcc
ffffd98a`36e4ca70 fffff805`76bd2d18 : ffffc98b`2f171080 000000f6`e77fee60 ffffc98b`1d6c9c00 ffffc98b`00000000 : nt!NtCreateWaitCompletionPacket+0xbf
ffffd98a`36e4cb00 00007ffc`d5cbd954 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
000000f6`e77fedc8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffc`d5cbd954
THREAD_SHA1_HASH_MOD_FUNC: 724bf577529b5411f8c8a84f3b74712c07109ce7
THREAD_SHA1_HASH_MOD_FUNC_OFFSET: a6e0dc93af22046c49afb7b8539a0ace601ace5a
THREAD_SHA1_HASH_MOD: 2a7ca9d3ab5386d53fea7498e1d81b9c4a4c036b
FOLLOWUP_IP:
nt!ObInsertObjectEx+cc
fffff805`76fdc59c f6474208 test byte ptr [rdi+42h],8
FAULT_INSTR_CODE: 84247f6
SYMBOL_STACK_INDEX: 0
SYMBOL_NAME: nt!ObInsertObjectEx+cc
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4efcf7a9
IMAGE_VERSION: 10.0.18362.476
STACK_COMMAND: .cxr 0xffffd98a36e4bdd0 ; kb
BUCKET_ID_FUNC_OFFSET: cc
FAILURE_BUCKET_ID: 0x3B_c0000005_nt!ObInsertObjectEx
BUCKET_ID: 0x3B_c0000005_nt!ObInsertObjectEx
PRIMARY_PROBLEM_CLASS: 0x3B_c0000005_nt!ObInsertObjectEx
TARGET_TIME: 2019-11-30T23:10:11.000Z
OSBUILD: 18362
OSSERVICEPACK: 476
SERVICEPACK_NUMBER: 0
OS_REVISION: 0
SUITE_MASK: 272
PRODUCT_TYPE: 1
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
OSEDITION: Windows 10 WinNt TerminalServer SingleUserTS
OS_LOCALE:
USER_LCID: 0
OSBUILD_TIMESTAMP: 2011-12-30 02:28:41
BUILDDATESTAMP_STR: 160101.0800
BUILDLAB_STR: WinBuild
BUILDOSVER_STR: 10.0.18362.476
ANALYSIS_SESSION_ELAPSED_TIME: 1665
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:0x3b_c0000005_nt!obinsertobjectex
FAILURE_ID_HASH: {81e179d5-1423-4bf6-d085-e8f692562c3a}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
SYSTEM_SERVICE_EXCEPTION (3b)
An exception happened while executing a system service routine.
Arguments:
Arg1: 00000000c0000005, Exception code that caused the bugcheck
Arg2: fffff8031e80e9c1, Address of the instruction which caused the bugcheck
Arg3: ffff8485bdd4cec0, Address of the context record for the exception that caused the bugcheck
Arg4: 0000000000000000, zero.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
PROCESSES_ANALYSIS: 1
SERVICE_ANALYSIS: 1
STACKHASH_ANALYSIS: 1
TIMELINE_ANALYSIS: 1
DUMP_CLASS: 1
DUMP_QUALIFIER: 400
BUILD_VERSION_STRING: 10.0.18362.476 (WinBuild.160101.0800)
SYSTEM_MANUFACTURER: Micro-Star International Co., Ltd
SYSTEM_PRODUCT_NAME: MS-7C02
SYSTEM_SKU: To be filled by O.E.M.
SYSTEM_VERSION: 1.0
BIOS_VENDOR: American Megatrends Inc.
BIOS_VERSION: 3.40
BIOS_DATE: 10/25/2019
BASEBOARD_MANUFACTURER: Micro-Star International Co., Ltd
BASEBOARD_PRODUCT: B450 TOMAHAWK MAX (MS-7C02)
BASEBOARD_VERSION: 1.0
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
DUMP_TYPE: 2
BUGCHECK_P1: c0000005
BUGCHECK_P2: fffff8031e80e9c1
BUGCHECK_P3: ffff8485bdd4cec0
BUGCHECK_P4: 0
EXCEPTION_CODE: (NTSTATUS) 0xc0000005 - <Unable to get error code text>
FAULTING_IP:
nt!ExpWnfUpdateSubscription+21
fffff803`1e80e9c1 48397818 cmp qword ptr [rax+18h],rdi
CONTEXT: ffff8485bdd4cec0 -- (.cxr 0xffff8485bdd4cec0)
rax=0000000000000086 rbx=ffffe10198966648 rcx=ffffe1019a4aaaa0
rdx=ffffe101989576f0 rsi=ffffe10198957740 rdi=ffffe1019a4aaaa0
rip=fffff8031e80e9c1 rsp=ffff8485bdd4d8b0 rbp=ffff8485bdd4d970
r8=0000000000000000 r9=0000000000000000 r10=ffffe10198957748
r11=0000000000000000 r12=0000000000000000 r13=0000000000000000
r14=ffff8d82b91aa3a0 r15=ffff8d82b3cde0c0
iopl=0 nv up ei pl nz ac pe cy
cs=0010 ss=0018 ds=002b es=002b fs=0053 gs=002b efl=00050213
nt!ExpWnfUpdateSubscription+0x21:
fffff803`1e80e9c1 48397818 cmp qword ptr [rax+18h],rdi ds:002b:00000000`0000009e=????????????????
Resetting default scope
BUGCHECK_STR: 0x3B_c0000005
CPU_COUNT: c
CPU_MHZ: e10
CPU_VENDOR: AuthenticAMD
CPU_FAMILY: 17
CPU_MODEL: 71
CPU_STEPPING: 0
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: WIN8_DRIVER_FAULT
PROCESS_NAME: svchost.exe
CURRENT_IRQL: 0
ANALYSIS_SESSION_HOST: DESKTOP-18V31A3
ANALYSIS_SESSION_TIME: 12-01-2019 13:12:40.0662
ANALYSIS_VERSION: 10.0.18362.1 x86fre
LAST_CONTROL_TRANSFER: from fffff8031e80e640 to fffff8031e80e9c1
STACK_TEXT:
ffff8485`bdd4d8b0 fffff803`1e80e640 : ffffffff`ffffffff ffff8485`bdd4d970 ffffe101`98957740 00000000`00000000 : nt!ExpWnfUpdateSubscription+0x21
ffff8485`bdd4d900 fffff803`1e80d5a3 : ffffe101`9a4aaaa0 ffff8d82`b3cde0c0 00000000`00000000 00000000`00000000 : nt!ExpWnfSubscribeNameInstance+0xcc
ffff8485`bdd4d9b0 fffff803`1e80d37b : ffff8485`bdd4db18 00000000`00000000 00000014`88fff450 00000014`ffffffff : nt!ExpWnfSubscribeWnfStateChange+0x1df
ffff8485`bdd4da90 fffff803`1e3d2d18 : ffff8d82`b91aa080 00000000`00000000 00000000`00000000 00000000`00000000 : nt!NtSubscribeWnfStateChange+0x8b
ffff8485`bdd4db00 00007ffb`16cbf734 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
00000014`88fff3f8 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffb`16cbf734
THREAD_SHA1_HASH_MOD_FUNC: c7d0a90ba0522d33e45aeaa012da6e1ec1fca33a
THREAD_SHA1_HASH_MOD_FUNC_OFFSET: eb5e167b621b28387a34f93b797a19ef982c6dcd
THREAD_SHA1_HASH_MOD: f08ac56120cad14894587db086f77ce277bfae84
FOLLOWUP_IP:
nt!ExpWnfUpdateSubscription+21
fffff803`1e80e9c1 48397818 cmp qword ptr [rax+18h],rdi
FAULT_INSTR_CODE: 18783948
SYMBOL_STACK_INDEX: 0
SYMBOL_NAME: nt!ExpWnfUpdateSubscription+21
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4efcf7a9
IMAGE_VERSION: 10.0.18362.476
STACK_COMMAND: .cxr 0xffff8485bdd4cec0 ; kb
BUCKET_ID_FUNC_OFFSET: 21
FAILURE_BUCKET_ID: 0x3B_c0000005_nt!ExpWnfUpdateSubscription
BUCKET_ID: 0x3B_c0000005_nt!ExpWnfUpdateSubscription
PRIMARY_PROBLEM_CLASS: 0x3B_c0000005_nt!ExpWnfUpdateSubscription
TARGET_TIME: 2019-11-30T16:12:05.000Z
OSBUILD: 18362
OSSERVICEPACK: 476
SERVICEPACK_NUMBER: 0
OS_REVISION: 0
SUITE_MASK: 272
PRODUCT_TYPE: 1
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
OSEDITION: Windows 10 WinNt TerminalServer SingleUserTS
OS_LOCALE:
USER_LCID: 0
OSBUILD_TIMESTAMP: 2011-12-30 02:28:41
BUILDDATESTAMP_STR: 160101.0800
BUILDLAB_STR: WinBuild
BUILDOSVER_STR: 10.0.18362.476
ANALYSIS_SESSION_ELAPSED_TIME: 180e
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:0x3b_c0000005_nt!expwnfupdatesubscription
FAILURE_ID_HASH: {63fadac6-2209-f083-1198-de28d6c77481}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
CRITICAL_STRUCTURE_CORRUPTION (109)
This bugcheck is generated when the kernel detects that critical kernel code or
data have been corrupted. There are generally three causes for a corruption:
1) A driver has inadvertently or deliberately modified critical kernel code
or data. See http://www.microsoft.com/whdc/driver/kernel/64bitPatching.mspx
2) A developer attempted to set a normal kernel breakpoint using a kernel
debugger that was not attached when the system was booted. Normal breakpoints,
"bp", can only be set if the debugger is attached at boot time. Hardware
breakpoints, "ba", can be set at any time.
3) A hardware corruption occurred, e.g. failing RAM holding kernel code or data.
Arguments:
Arg1: a39ffcd918c8b517, Reserved
Arg2: b3b7095f6b46fdc8, Reserved
Arg3: fffff8071bb11000, Failure type dependent information
Arg4: 0000000000000001, Type of corrupted region, can be
0 : A generic data region
1 : Modification of a function or .pdata
2 : A processor IDT
3 : A processor GDT
4 : Type 1 process list corruption
5 : Type 2 process list corruption
6 : Debug routine modification
7 : Critical MSR modification
8 : Object type
9 : A processor IVT
a : Modification of a system service function
b : A generic session data region
c : Modification of a session function or .pdata
d : Modification of an import table
e : Modification of a session import table
f : Ps Win32 callout modification
10 : Debug switch routine modification
11 : IRP allocator modification
12 : Driver call dispatcher modification
13 : IRP completion dispatcher modification
14 : IRP deallocator modification
15 : A processor control register
16 : Critical floating point control register modification
17 : Local APIC modification
18 : Kernel notification callout modification
19 : Loaded module list modification
1a : Type 3 process list corruption
1b : Type 4 process list corruption
1c : Driver object corruption
1d : Executive callback object modification
1e : Modification of module padding
1f : Modification of a protected process
20 : A generic data region
21 : A page hash mismatch
22 : A session page hash mismatch
23 : Load config directory modification
24 : Inverted function table modification
25 : Session configuration modification
26 : An extended processor control register
27 : Type 1 pool corruption
28 : Type 2 pool corruption
29 : Type 3 pool corruption
2a : Type 4 pool corruption
2b : Modification of a function or .pdata
2c : Image integrity corruption
2d : Processor misconfiguration
2e : Type 5 process list corruption
2f : Process shadow corruption
30 : Retpoline code page corruption
101 : General pool corruption
102 : Modification of win32k.sys
Debugging Details:
------------------
KEY_VALUES_STRING: 1
PROCESSES_ANALYSIS: 1
SERVICE_ANALYSIS: 1
STACKHASH_ANALYSIS: 1
TIMELINE_ANALYSIS: 1
DUMP_CLASS: 1
DUMP_QUALIFIER: 400
BUILD_VERSION_STRING: 10.0.18362.476 (WinBuild.160101.0800)
SYSTEM_MANUFACTURER: Micro-Star International Co., Ltd
SYSTEM_PRODUCT_NAME: MS-7C02
SYSTEM_SKU: To be filled by O.E.M.
SYSTEM_VERSION: 1.0
BIOS_VENDOR: American Megatrends Inc.
BIOS_VERSION: 3.40
BIOS_DATE: 10/25/2019
BASEBOARD_MANUFACTURER: Micro-Star International Co., Ltd
BASEBOARD_PRODUCT: B450 TOMAHAWK MAX (MS-7C02)
BASEBOARD_VERSION: 1.0
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
DUMP_TYPE: 2
BUGCHECK_P1: a39ffcd918c8b517
BUGCHECK_P2: b3b7095f6b46fdc8
BUGCHECK_P3: fffff8071bb11000
BUGCHECK_P4: 1
PG_MISMATCH: 3ECC0DDC
FAULTING_IP:
nt!Ports <PERF> (nt+0x511000)+0
fffff807`1bb11000 1010 adc byte ptr [rax],dl
CPU_COUNT: c
CPU_MHZ: e10
CPU_VENDOR: AuthenticAMD
CPU_FAMILY: 17
CPU_MODEL: 71
CPU_STEPPING: 0
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: WIN8_DRIVER_FAULT
BUGCHECK_STR: 0x109
PROCESS_NAME: csrss.exe
CURRENT_IRQL: 2
ANALYSIS_SESSION_HOST: DESKTOP-18V31A3
ANALYSIS_SESSION_TIME: 12-01-2019 13:12:36.0572
ANALYSIS_VERSION: 10.0.18362.1 x86fre
STACK_TEXT:
fffff586`a1f30e98 00000000`00000000 : 00000000`00000109 a39ffcd9`18c8b517 b3b7095f`6b46fdc8 fffff807`1bb11000 : nt!KeBugCheckEx
THREAD_SHA1_HASH_MOD_FUNC: 81a83ae0317433a47fcc36991983df3b6e638b71
THREAD_SHA1_HASH_MOD_FUNC_OFFSET: 6e16edd8c7dd677734fdbcd2397a2e35e9fae964
THREAD_SHA1_HASH_MOD: 76cd06466d098060a9eb26e5fd2a25cb1f3fe0a3
FOLLOWUP_IP:
nt!Ports <PERF> (nt+0x511000)+0
fffff807`1bb11000 1010 adc byte ptr [rax],dl
FAULT_INSTR_CODE: 1010
SYMBOL_NAME: nt!Ports <PERF> (nt+0x511000)+0
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
DEBUG_FLR_IMAGE_TIMESTAMP: 4efcf7a9
IMAGE_VERSION: 10.0.18362.476
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 0
FAILURE_BUCKET_ID: 0x109_1_nt!Ports__PERF__(nt+0x511000)
BUCKET_ID: 0x109_1_nt!Ports__PERF__(nt+0x511000)
PRIMARY_PROBLEM_CLASS: 0x109_1_nt!Ports__PERF__(nt+0x511000)
TARGET_TIME: 2019-11-30T10:23:56.000Z
OSBUILD: 18362
OSSERVICEPACK: 476
SERVICEPACK_NUMBER: 0
OS_REVISION: 0
SUITE_MASK: 272
PRODUCT_TYPE: 1
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
OSEDITION: Windows 10 WinNt TerminalServer SingleUserTS
OS_LOCALE:
USER_LCID: 0
OSBUILD_TIMESTAMP: 2011-12-30 02:28:41
BUILDDATESTAMP_STR: 160101.0800
BUILDLAB_STR: WinBuild
BUILDOSVER_STR: 10.0.18362.476
ANALYSIS_SESSION_ELAPSED_TIME: d25
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:0x109_1_nt!ports__perf__(nt+0x511000)
FAILURE_ID_HASH: {6f07dceb-751e-bee2-a72d-959161a93c09}
Followup: MachineOwner
---------
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
KERNEL_SECURITY_CHECK_FAILURE (139)
A kernel component has corrupted a critical data structure. The corruption
could potentially allow a malicious user to gain control of this machine.
Arguments:
Arg1: 0000000000000003, A LIST_ENTRY has been corrupted (i.e. double remove).
Arg2: ffffc7075a3b1300, Address of the trap frame for the exception that caused the bugcheck
Arg3: ffffc7075a3b1258, Address of the exception record for the exception that caused the bugcheck
Arg4: 0000000000000000, Reserved
Debugging Details:
------------------
*** WARNING: Unable to verify timestamp for adgnetworktdidrv.sys
KEY_VALUES_STRING: 1
PROCESSES_ANALYSIS: 1
SERVICE_ANALYSIS: 1
STACKHASH_ANALYSIS: 1
TIMELINE_ANALYSIS: 1
DUMP_CLASS: 1
DUMP_QUALIFIER: 400
BUILD_VERSION_STRING: 10.0.18362.476 (WinBuild.160101.0800)
SYSTEM_MANUFACTURER: Micro-Star International Co., Ltd
SYSTEM_PRODUCT_NAME: MS-7C02
SYSTEM_SKU: To be filled by O.E.M.
SYSTEM_VERSION: 1.0
BIOS_VENDOR: American Megatrends Inc.
BIOS_VERSION: 3.40
BIOS_DATE: 10/25/2019
BASEBOARD_MANUFACTURER: Micro-Star International Co., Ltd
BASEBOARD_PRODUCT: B450 TOMAHAWK MAX (MS-7C02)
BASEBOARD_VERSION: 1.0
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
DUMP_TYPE: 2
BUGCHECK_P1: 3
BUGCHECK_P2: ffffc7075a3b1300
BUGCHECK_P3: ffffc7075a3b1258
BUGCHECK_P4: 0
TRAP_FRAME: ffffc7075a3b1300 -- (.trap 0xffffc7075a3b1300)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=ffffb586c760129a rbx=0000000000000000 rcx=0000000000000003
rdx=ffffb586c76012b0 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8013dbf514b rsp=ffffc7075a3b1490 rbp=ffffc7075a3b1590
r8=ffffb586c7601288 r9=ffffb586c7601298 r10=ffffb586c93fe000
r11=ffffb586c7601040 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz na po cy
nt!RtlpHpLfhSlotAllocate+0x1c190b:
fffff801`3dbf514b cd29 int 29h
Resetting default scope
EXCEPTION_RECORD: ffffc7075a3b1258 -- (.exr 0xffffc7075a3b1258)
ExceptionAddress: fffff8013dbf514b (nt!RtlpHpLfhSlotAllocate+0x00000000001c190b)
ExceptionCode: c0000409 (Security check failure or stack buffer overrun)
ExceptionFlags: 00000001
NumberParameters: 1
Parameter[0]: 0000000000000003
Subcode: 0x3 FAST_FAIL_CORRUPT_LIST_ENTRY
CPU_COUNT: c
CPU_MHZ: e10
CPU_VENDOR: AuthenticAMD
CPU_FAMILY: 17
CPU_MODEL: 71
CPU_STEPPING: 0
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
BUGCHECK_STR: 0x139
PROCESS_NAME: AdguardSvc.exe
CURRENT_IRQL: 2
DEFAULT_BUCKET_ID: FAIL_FAST_CORRUPT_LIST_ENTRY
ERROR_CODE: (NTSTATUS) 0xc0000409 - <Unable to get error code text>
EXCEPTION_CODE: (NTSTATUS) 0xc0000409 - <Unable to get error code text>
EXCEPTION_CODE_STR: c0000409
EXCEPTION_PARAMETER1: 0000000000000003
ANALYSIS_SESSION_HOST: DESKTOP-18V31A3
ANALYSIS_SESSION_TIME: 12-01-2019 13:12:32.0710
ANALYSIS_VERSION: 10.0.18362.1 x86fre
LAST_CONTROL_TRANSFER: from fffff8013dbd32e9 to fffff8013dbc14e0
STACK_TEXT:
ffffc707`5a3b0fd8 fffff801`3dbd32e9 : 00000000`00000139 00000000`00000003 ffffc707`5a3b1300 ffffc707`5a3b1258 : nt!KeBugCheckEx
ffffc707`5a3b0fe0 fffff801`3dbd3710 : 00000000`00000001 ffffca81`263d9180 00000000`00000000 00000000`00000000 : nt!KiBugCheckDispatch+0x69
ffffc707`5a3b1120 fffff801`3dbd1aa5 : 00000000`00000000 fffff801`3e01feb3 ffffc707`5a3b15c0 00000000`00000001 : nt!KiFastFailDispatch+0xd0
ffffc707`5a3b1300 fffff801`3dbf514b : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00989680 : nt!KiRaiseSecurityCheckFailure+0x325
ffffc707`5a3b1490 fffff801`3da33294 : ffffb586`c7600340 ffffb586`c7601040 ffffb586`c7601280 ffffb586`00000130 : nt!RtlpHpLfhSlotAllocate+0x1c190b
ffffc707`5a3b15f0 fffff801`3dd6f06d : ffffb586`00000000 00000000`00000000 00000000`00000000 00000000`0000011b : nt!ExAllocateHeapPool+0xb94
ffffc707`5a3b1730 fffff801`48ba83c7 : 00000000`00000000 00000000`00000000 00000000`00000010 fffff9e5`00000000 : nt!ExAllocatePoolWithTag+0x5d
ffffc707`5a3b1780 00000000`00000000 : 00000000`00000000 00000000`00000010 fffff9e5`00000000 00000000`00000006 : adgnetworktdidrv+0x83c7
THREAD_SHA1_HASH_MOD_FUNC: 1d4a1ec3ad0af96c55913bb61d0851faad07c009
THREAD_SHA1_HASH_MOD_FUNC_OFFSET: 4c4fa919898c3b1a3191fbf269c39e2fe9793265
THREAD_SHA1_HASH_MOD: fc0fd1c8b1fd561290d1c915d05d4dc50539053b
FOLLOWUP_IP:
adgnetworktdidrv+83c7
fffff801`48ba83c7 ?? ???
SYMBOL_STACK_INDEX: 7
SYMBOL_NAME: adgnetworktdidrv+83c7
FOLLOWUP_NAME: MachineOwner
MODULE_NAME: adgnetworktdidrv
IMAGE_NAME: adgnetworktdidrv.sys
DEBUG_FLR_IMAGE_TIMESTAMP: 5d52ce4b
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 83c7
FAILURE_BUCKET_ID: 0x139_3_CORRUPT_LIST_ENTRY_adgnetworktdidrv!unknown_function
BUCKET_ID: 0x139_3_CORRUPT_LIST_ENTRY_adgnetworktdidrv!unknown_function
PRIMARY_PROBLEM_CLASS: 0x139_3_CORRUPT_LIST_ENTRY_adgnetworktdidrv!unknown_function
TARGET_TIME: 2019-11-29T16:04:51.000Z
OSBUILD: 18362
OSSERVICEPACK: 476
SERVICEPACK_NUMBER: 0
OS_REVISION: 0
SUITE_MASK: 272
PRODUCT_TYPE: 1
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
OSEDITION: Windows 10 WinNt TerminalServer SingleUserTS
OS_LOCALE:
USER_LCID: 0
OSBUILD_TIMESTAMP: 2011-12-30 02:28:41
BUILDDATESTAMP_STR: 160101.0800
BUILDLAB_STR: WinBuild
BUILDOSVER_STR: 10.0.18362.476
ANALYSIS_SESSION_ELAPSED_TIME: dfa
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:0x139_3_corrupt_list_entry_adgnetworktdidrv!unknown_function
FAILURE_ID_HASH: {09ba5999-f8c9-31c4-c50b-242b67147646}
Followup: MachineOwner
---------
9: kd> lmvm adgnetworktdidrv
Browse full module list
start end module name
fffff801`48ba0000 fffff801`48bb4000 adgnetworktdidrv T (no symbols)
Loaded symbol image file: adgnetworktdidrv.sys
Image path: adgnetworktdidrv.sys
Image name: adgnetworktdidrv.sys
Browse all global symbols functions data
Timestamp: Tue Aug 13 07:50:51 2019 (5D52CE4B)
CheckSum: 000175EB
ImageSize: 00014000
Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4
Information from resource tables:
*******************************************************************************
* *
* Bugcheck Analysis *
* *
*******************************************************************************
SYSTEM_SERVICE_EXCEPTION (3b)
An exception happened while executing a system service routine.
Arguments:
Arg1: 00000000c0000005, Exception code that caused the bugcheck
Arg2: fffff8051a917d4e, Address of the instruction which caused the bugcheck
Arg3: ffffba0458fb7290, Address of the context record for the exception that caused the bugcheck
Arg4: 0000000000000000, zero.
Debugging Details:
------------------
KEY_VALUES_STRING: 1
PROCESSES_ANALYSIS: 1
SERVICE_ANALYSIS: 1
STACKHASH_ANALYSIS: 1
TIMELINE_ANALYSIS: 1
DUMP_CLASS: 1
DUMP_QUALIFIER: 400
BUILD_VERSION_STRING: 10.0.18362.476 (WinBuild.160101.0800)
SYSTEM_MANUFACTURER: Micro-Star International Co., Ltd
SYSTEM_PRODUCT_NAME: MS-7C02
SYSTEM_SKU: To be filled by O.E.M.
SYSTEM_VERSION: 1.0
BIOS_VENDOR: American Megatrends Inc.
BIOS_VERSION: 3.40
BIOS_DATE: 10/25/2019
BASEBOARD_MANUFACTURER: Micro-Star International Co., Ltd
BASEBOARD_PRODUCT: B450 TOMAHAWK MAX (MS-7C02)
BASEBOARD_VERSION: 1.0
DUMP_FILE_ATTRIBUTES: 0x8
Kernel Generated Triage Dump
DUMP_TYPE: 2
BUGCHECK_P1: c0000005
BUGCHECK_P2: fffff8051a917d4e
BUGCHECK_P3: ffffba0458fb7290
BUGCHECK_P4: 0
EXCEPTION_CODE: (NTSTATUS) 0xc0000005 - <Unable to get error code text>
FAULTING_IP:
nt!RtlFnToFxFrame+8e
fffff805`1a917d4e 8b5c2508 mov ebx,dword ptr [rbp+8]
CONTEXT: ffffba0458fb7290 -- (.cxr 0xffffba0458fb7290)
rax=000000000000c000 rbx=000000000000ffff rcx=ffffba0458fb7e4f
rdx=ffffba0458fb826c rsi=ffffba0458fb8570 rdi=000000000000c000
rip=fffff8051a917d4e rsp=ffffba0458fb7c88 rbp=000000000001003f
r8=ffffba0458fb7d50 r9=0000000000000000 r10=0000000000000001
r11=ffffba0458fb7e80 r12=0000000000000023 r13=ffffe5896bfe4080
r14=ffffba0458fb8540 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
cs=0010 ss=0018 ds=002b es=002b fs=0053 gs=002b efl=00050297
nt!RtlFnToFxFrame+0x8e:
fffff805`1a917d4e 8b5c2508 mov ebx,dword ptr [rbp+8] ss:0018:00000000`00010047=????????
Resetting default scope
BUGCHECK_STR: 0x3B_c0000005
CPU_COUNT: c
CPU_MHZ: e10
CPU_VENDOR: AuthenticAMD
CPU_FAMILY: 17
CPU_MODEL: 71
CPU_STEPPING: 0
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
DEFAULT_BUCKET_ID: CODE_CORRUPTION
PROCESS_NAME: Adguard.exe
CURRENT_IRQL: 0
ANALYSIS_SESSION_HOST: DESKTOP-18V31A3
ANALYSIS_SESSION_TIME: 12-01-2019 13:14:20.0723
ANALYSIS_VERSION: 10.0.18362.1 x86fre
LAST_CONTROL_TRANSFER: from fffff8051aec28b5 to fffff8051a917d4e
STACK_TEXT:
ffffba04`58fb7c88 fffff805`1aec28b5 : ffffba04`58fb8250 00000000`00010038 ffffba04`58fb8ac8 ffffba04`58fb8ac0 : nt!RtlFnToFxFrame+0x8e
ffffba04`58fb7c90 fffff805`1aec2634 : 00000000`00000033 ffff2ed3`9721cd48 ffffba04`58fb8250 ffffba04`58fb7d50 : nt!RtlpWow64CtxToAmd64+0xe5
ffffba04`58fb7cc0 fffff805`1aec187f : 0fffffff`fffffff0 ffffba04`58fb8540 00000000`00010040 00000000`0001003f : nt!RtlpWow64SetContextOnAmd64+0x48
ffffba04`58fb7d00 fffff805`1ade8179 : ffffba04`58fb8b00 ffffce00`000074f8 00000000`00e9fc4c ffffce67`33800000 : nt!PspWow64SetContextThread+0x267
ffffba04`58fb8890 fffff805`1a9d2d18 : ffffe589`6bfe4080 00000000`7782dc00 00000000`00000000 ffffe589`68c12460 : nt!NtSetInformationThread+0xb39
ffffba04`58fb8b00 00007ffd`db9fc264 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
00000000`00e5e898 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : 0x00007ffd`db9fc264
CHKIMG_EXTENSION: !chkimg -lo 50 -db !nt
64 errors : !nt (fffff8051a917140-fffff8051a917ff8)
fffff8051a917140 *50 0f 46 c1 33 d2 8d 71 *f6 03 f0 8b c6 f7 f1 2b P.F.3..q.......+
fffff8051a917150 *f0 44 39 1d d0 44 32 00 *61 8b c3 74 45 42 0f b6 .D9..D2.a..tEB..
fffff8051a917160 *2c 23 77 b8 1f 85 eb 51 *44 0f af c9 83 c1 32 f7 ,#w....QD.....2.
fffff8051a917170 *24 0f b6 0d 78 d8 32 00 44 8b c2 33 d2 41 c1 e8 $...x.2.D..3.A..
fffff8051a917180 *11 45 2b c8 41 8b c1 f7 *b1 41 8b c3 44 03 c2 41 .E+.A....A..D..A
fffff8051a917190 *1b f0 73 0e b8 40 00 00 *20 41 8b f0 44 8b f0 89 ..s..@.. A..D...
fffff8051a9171a0 *68 50 8b d8 45 85 d2 75 1f 44 38 9f 8b 00 00 00 hP..E..u.D8.....
fffff8051a9171b0 *fd 16 0f b6 b7 80 00 00 *49 44 8b f0 41 0f ba ee ........ID..A...
...
fffff8051a917300 *15 55 48 8b 12 48 8b c2 *dd 8b ca 48 d1 e8 48 23 .UH..H.....H..H#
fffff8051a917310 *f5 48 2b d0 48 b8 33 33 *73 33 33 33 33 33 48 8b .H+.H.33s33333H.
fffff8051a917320 *c8 48 23 d0 48 c1 e9 02 *3d 23 c8 48 03 ca 48 8b .H#.H...=#.H..H.
fffff8051a917330 *50 48 c1 e8 04 48 03 c1 *d8 b9 0f 0f 0f 0f 0f 0f PH...H..........
...
fffff8051a9173c0 *b7 55 68 4d 8b cf 41 88 *14 3c 8f 00 00 00 4c 8b .UhM..A..<....L.
fffff8051a9173d0 *76 8b 45 50 48 8b cf 89 *52 24 28 40 88 74 24 20 v.EPH...R$(@.t$
fffff8051a9173e0 *f8 9b c4 1e 00 44 8b 55 68 49 ff c4 48 8b 45 b8 .....D.UhI..H.E.
fffff8051a9173f0 *ab ff c2 8b 75 60 48 83 *78 08 48 8b 5d c0 41 bb ....u`H.x.H.].A.
...
fffff8051a917b80 *cf cc cc cc cc cc cc cc *8e cc cc cc cc cc cc cc ................
fffff8051a917b90 48 83 ec 38 48 89 4c 24 *34 4c 8d 44 24 20 48 89 H..8H.L$4L.D$ H.
fffff8051a917ba0 *58 24 28 33 c9 48 8d 15 *fc 5e ff ff 41 b9 01 00 X$(3.H...^..A...
fffff8051a917bb0 *4c 00 e8 c5 5b f4 ff 48 *a4 c4 38 c3 cc cc cc cc L...[..H..8.....
...
fffff8051a917d40 *e0 c1 e3 02 41 ff c2 41 *81 fa 08 72 c2 48 8b 5c ....A..A...r.H.\
fffff8051a917d50 *25 08 48 8b 7c 24 10 44 *89 49 04 c3 cc cc cc cc %.H.|$.D.I......
fffff8051a917d60 cd cc cc cc 48 89 7c 24 *e9 4c 89 64 24 10 4c 89 ....H.|$.L.d$.L.
fffff8051a917d70 6c 24 18 55 41 56 41 57 *6c 8b ec 48 83 ec 40 4c l$.UAVAWl..H..@L
fffff8051a917d80 *cb 79 10 33 c0 48 89 45 *a0 4c 8b e2 48 89 45 e8 .y.3.H.E.L..H.E.
fffff8051a917d90 *6a 89 45 f0 4d 85 ff 0f *a0 36 01 00 00 4d 8b 7f j.E.M....6...M..
fffff8051a917da0 *8d 48 8d 55 e0 48 8d 0d *0c d2 3d 00 e8 8f 70 f2 .H.U.H....=...p.
fffff8051a917db0 *cf 48 8b 05 68 df 34 00 *cc 8d 2d 61 df 34 00 49 .H..h.4...-a.4.I
...
fffff8051a917f00 *02 83 e0 04 c3 b8 01 00 *70 00 c3 b8 02 00 00 00 ........p.......
fffff8051a917f10 *54 b8 03 00 00 00 c3 cc cc cc cc cc cc cc cc cc T...............
fffff8051a917f20 7a 8b c4 48 89 58 08 48 *df 68 10 48 89 70 20 57 z..H.X.H.h.H.p W
fffff8051a917f30 *4c 83 ec 20 48 8b 3d b5 *d4 31 00 33 db 48 89 58 L.. H.=..1.3.H.X
...
fffff8051a917fc0 *6f bd 01 00 00 00 44 0f *ff 49 04 4c 8b e2 44 0f o.....D..I.L..D.
fffff8051a917fd0 *b5 01 41 8b d9 0f bf 71 *14 41 2b dd 44 0f bf 71 ..A....q.A+.D..q
fffff8051a917fe0 *3b 8b f8 44 0f bf 79 0a *54 8d 50 ff 0f bf 69 0c ;..D..y.T.P...i.
fffff8051a917ff0 *7c 41 3b c5 0f 8c b2 01 *aa 00 66 45 3b cd 0f 8c |A;.......fE;...
MODULE_NAME: memory_corruption
IMAGE_NAME: memory_corruption
FOLLOWUP_NAME: memory_corruption
DEBUG_FLR_IMAGE_TIMESTAMP: 0
MEMORY_CORRUPTOR: STRIDE
STACK_COMMAND: .cxr 0xffffba0458fb7290 ; kb
FAILURE_BUCKET_ID: MEMORY_CORRUPTION_STRIDE
BUCKET_ID: MEMORY_CORRUPTION_STRIDE
PRIMARY_PROBLEM_CLASS: MEMORY_CORRUPTION_STRIDE
TARGET_TIME: 2019-11-29T15:29:55.000Z
OSBUILD: 18362
OSSERVICEPACK: 476
SERVICEPACK_NUMBER: 0
OS_REVISION: 0
SUITE_MASK: 272
PRODUCT_TYPE: 1
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
OSEDITION: Windows 10 WinNt TerminalServer SingleUserTS
OS_LOCALE:
USER_LCID: 0
OSBUILD_TIMESTAMP: 2011-12-30 02:28:41
BUILDDATESTAMP_STR: 160101.0800
BUILDLAB_STR: WinBuild
BUILDOSVER_STR: 10.0.18362.476
ANALYSIS_SESSION_ELAPSED_TIME: 25a7
ANALYSIS_SOURCE: KM
FAILURE_ID_HASH_STRING: km:memory_corruption_stride
FAILURE_ID_HASH: {574dbc1b-92cb-fb09-cb7a-cacc1bb2c511}
Followup: memory_corruption
---------