DPC_WATCHDOG_VIOLATION (133)
The DPC watchdog detected a prolonged run time at an IRQL of DISPATCH_LEVEL
or above.
Arguments:
Arg1: 0000000000000001, The system cumulatively spent an extended period of time at
DISPATCH_LEVEL or above. The offending component can usually be
identified with a stack trace.
Arg2: 0000000000001e00, The watchdog period.
Arg3: fffff801764fb320, cast to nt!DPC_WATCHDOG_GLOBAL_TRIAGE_BLOCK, which contains
additional information regarding the cumulative timeout
Arg4: 0000000000000000
Debugging Details:
------------------
*************************************************************************
*** ***
*** ***
*** Either you specified an unqualified symbol, or your debugger ***
*** doesn't have full symbol information. Unqualified symbol ***
*** resolution is turned off by default. Please either specify a ***
*** fully qualified symbol module!symbolname, or enable resolution ***
*** of unqualified symbols by typing ".symopt- 100". Note that ***
*** enabling unqualified symbol resolution with network symbol ***
*** server shares in the symbol path may cause the debugger to ***
*** appear to hang for long periods of time when an incorrect ***
*** symbol name is typed or the network symbol server is down. ***
*** ***
*** For some commands to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: TickPeriods ***
*** ***
*************************************************************************
*** WARNING: Unable to verify timestamp for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 5515
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on BORA
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 52444
Key : Analysis.Memory.CommitPeak.Mb
Value: 77
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 133
BUGCHECK_P1: 1
BUGCHECK_P2: 1e00
BUGCHECK_P3: fffff801764fb320
BUGCHECK_P4: 0
DPC_TIMEOUT_TYPE: DPC_QUEUE_EXECUTION_TIMEOUT_EXCEEDED
TRAP_FRAME: fffff8017b06bc00 -- (.trap 0xfffff8017b06bc00)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000000 rbx=0000000000000000 rcx=ffffd287b25f5502
rdx=0000000000000002 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80175b42e3b rsp=fffff8017b06bd90 rbp=0000000000000000
r8=0000000000000000 r9=0000000000000000 r10=0000000000000002
r11=fffff8017b06bd40 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl zr na po nc
nt!KzLowerIrql+0x1b:
fffff801`75b42e3b 4883c420 add rsp,20h
Resetting default scope
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
STACK_TEXT:
fffff801`7b07ae18 fffff801`75c873f6 : 00000000`00000133 00000000`00000001 00000000`00001e00 fffff801`764fb320 : nt!KeBugCheckEx
fffff801`7b07ae20 fffff801`75b26853 : 0000101e`a0d45cb7 fffff801`73119180 00000000`00000000 fffff801`73119180 : nt!KeAccumulateTicks+0x15e346
fffff801`7b07ae80 fffff801`75b2633a : fffff801`764f38c0 fffff801`7b06bc80 fffff801`7a1edf00 00000000`00005002 : nt!KeClockInterruptNotify+0x453
fffff801`7b07af30 fffff801`75a2ecd5 : fffff801`764f38c0 fffff801`7b07af40 00000000`00000010 ffffc57e`efbf068f : nt!HalpTimerClockIpiRoutine+0x1a
fffff801`7b07af60 fffff801`75bf6cba : fffff801`7b06bc80 fffff801`764f38c0 00000000`00000000 00000000`00000000 : nt!KiCallInterruptServiceRoutine+0xa5
fffff801`7b07afb0 fffff801`75bf7227 : 00000000`00000002 fffff801`75bf7234 00000000`00000000 ffffd287`b244ea02 : nt!KiInterruptSubDispatchNoLockNoEtw+0xfa
fffff801`7b06bc00 fffff801`75b42e3b : fffff801`88eaa8f0 00000000`00000000 00000000`00400100 00000000`00000000 : nt!KiInterruptDispatchNoLockNoEtw+0x37
fffff801`7b06bd90 fffff801`88939d5c : ffffd287`b659b000 fffff801`7b06be40 ffffd287`b2bed720 fffff801`88a0c4bd : nt!KzLowerIrql+0x1b
fffff801`7b06bdc0 ffffd287`b659b000 : fffff801`7b06be40 ffffd287`b2bed720 fffff801`88a0c4bd ffffd287`00000000 : nvlddmkm+0x1f9d5c
fffff801`7b06bdc8 fffff801`7b06be40 : ffffd287`b2bed720 fffff801`88a0c4bd ffffd287`00000000 fffff801`8895e3dc : 0xffffd287`b659b000
fffff801`7b06bdd0 ffffd287`b2bed720 : fffff801`88a0c4bd ffffd287`00000000 fffff801`8895e3dc ffffd287`00000000 : 0xfffff801`7b06be40
fffff801`7b06bdd8 fffff801`88a0c4bd : ffffd287`00000000 fffff801`8895e3dc ffffd287`00000000 00000000`ffffffff : 0xffffd287`b2bed720
fffff801`7b06bde0 ffffd287`00000000 : fffff801`8895e3dc ffffd287`00000000 00000000`ffffffff 00000000`ffffffff : nvlddmkm+0x2cc4bd
fffff801`7b06bde8 fffff801`8895e3dc : ffffd287`00000000 00000000`ffffffff 00000000`ffffffff 00000000`00000000 : 0xffffd287`00000000
fffff801`7b06bdf0 ffffd287`00000000 : 00000000`ffffffff 00000000`ffffffff 00000000`00000000 ffffd287`b63b5c30 : nvlddmkm+0x21e3dc
fffff801`7b06bdf8 00000000`ffffffff : 00000000`ffffffff 00000000`00000000 ffffd287`b63b5c30 fffff801`88a0af12 : 0xffffd287`00000000
fffff801`7b06be00 00000000`ffffffff : 00000000`00000000 ffffd287`b63b5c30 fffff801`88a0af12 ffffd287`b2bed720 : 0xffffffff
fffff801`7b06be08 00000000`00000000 : ffffd287`b63b5c30 fffff801`88a0af12 ffffd287`b2bed720 00000000`00000000 : 0xffffffff
SYMBOL_NAME: nvlddmkm+1f9d5c
MODULE_NAME: nvlddmkm
IMAGE_NAME: nvlddmkm.sys
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 1f9d5c
FAILURE_BUCKET_ID: 0x133_ISR_nvlddmkm!unknown_function
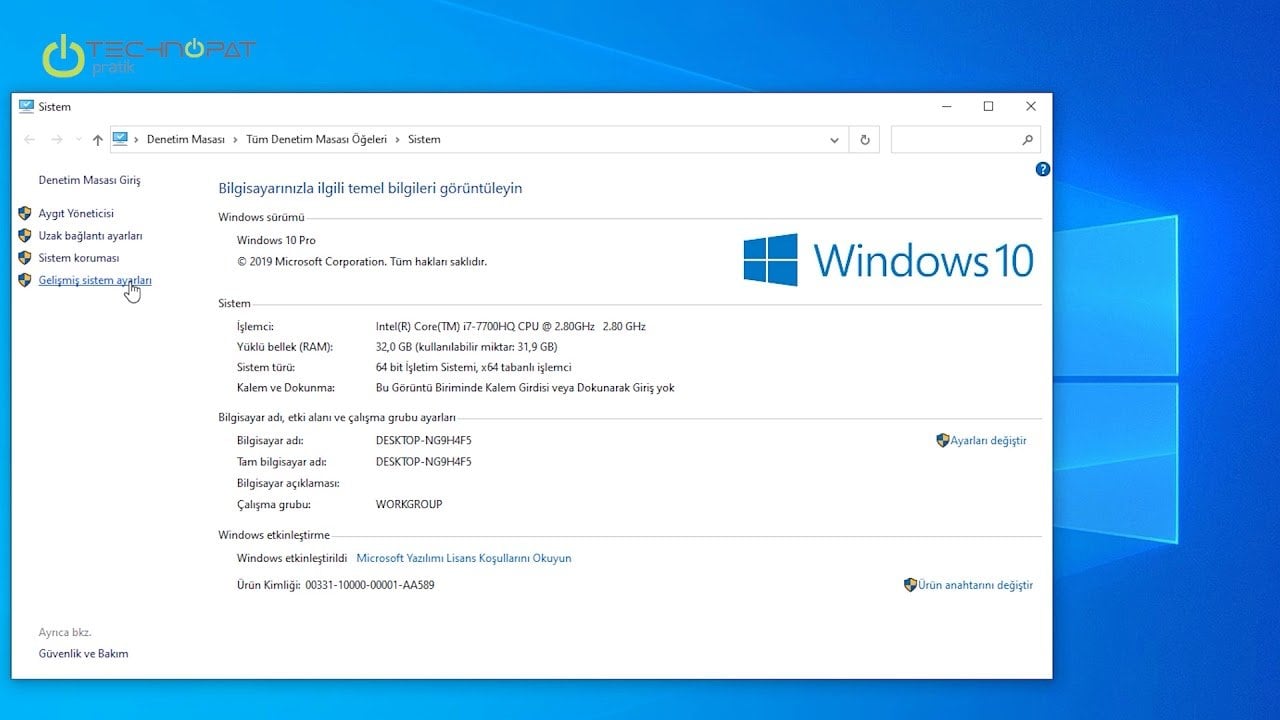
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {f97493a5-ea2b-23ca-a808-8602773c2a86}
Followup: MachineOwner
---------
DPC_WATCHDOG_VIOLATION (133)
The DPC watchdog detected a prolonged run time at an IRQL of DISPATCH_LEVEL
or above.
Arguments:
Arg1: 0000000000000001, The system cumulatively spent an extended period of time at
DISPATCH_LEVEL or above. The offending component can usually be
identified with a stack trace.
Arg2: 0000000000001e00, The watchdog period.
Arg3: fffff80340efb320, cast to nt!DPC_WATCHDOG_GLOBAL_TRIAGE_BLOCK, which contains
additional information regarding the cumulative timeout
Arg4: 0000000000000000
Debugging Details:
------------------
*************************************************************************
*** ***
*** ***
*** Either you specified an unqualified symbol, or your debugger ***
*** doesn't have full symbol information. Unqualified symbol ***
*** resolution is turned off by default. Please either specify a ***
*** fully qualified symbol module!symbolname, or enable resolution ***
*** of unqualified symbols by typing ".symopt- 100". Note that ***
*** enabling unqualified symbol resolution with network symbol ***
*** server shares in the symbol path may cause the debugger to ***
*** appear to hang for long periods of time when an incorrect ***
*** symbol name is typed or the network symbol server is down. ***
*** ***
*** For some commands to work properly, your symbol path ***
*** must point to .pdb files that have full type information. ***
*** ***
*** Certain .pdb files (such as the public OS symbols) do not ***
*** contain the required information. Contact the group that ***
*** provided you with these symbols if you need this command to ***
*** work. ***
*** ***
*** Type referenced: TickPeriods ***
*** ***
*************************************************************************
*** WARNING: Unable to verify timestamp for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 6156
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on BORA
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 46781
Key : Analysis.Memory.CommitPeak.Mb
Value: 76
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: 133
BUGCHECK_P1: 1
BUGCHECK_P2: 1e00
BUGCHECK_P3: fffff80340efb320
BUGCHECK_P4: 0
DPC_TIMEOUT_TYPE: DPC_QUEUE_EXECUTION_TIMEOUT_EXCEEDED
TRAP_FRAME: fffff80343a6abe0 -- (.trap 0xfffff80343a6abe0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000000000000000 rbx=0000000000000000 rcx=ffffcd0ffacfad02
rdx=0000000000000002 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8035026d9e6 rsp=fffff80343a6ad70 rbp=0000000000000000
r8=0000000000000001 r9=0000000000000000 r10=0000000000000000
r11=000000000000000e r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei pl zr na po nc
nvlddmkm+0x20d9e6:
fffff803`5026d9e6 89442470 mov dword ptr [rsp+70h],eax ss:0018:fffff803`43a6ade0=00000000
Resetting default scope
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
STACK_TEXT:
fffff803`43a79e18 fffff803`40687a98 : 00000000`00000133 00000000`00000001 00000000`00001e00 fffff803`40efb320 : nt!KeBugCheckEx
fffff803`43a79e20 fffff803`40526993 : 00000b76`5a1cf130 fffff803`3bd17180 00000000`00000000 fffff803`3bd17180 : nt!KeAccumulateTicks+0x15dda8
fffff803`43a79e80 fffff803`4052647a : fffff803`40ef38c0 fffff803`43a6ac60 fffff803`4d633c00 00000000`00006102 : nt!KeClockInterruptNotify+0x453
fffff803`43a79f30 fffff803`4042ecd5 : fffff803`40ef38c0 fffff803`43a79f40 00000000`00000010 ffff94f5`c3a75d05 : nt!HalpTimerClockIpiRoutine+0x1a
fffff803`43a79f60 fffff803`405f604a : fffff803`43a6ac60 fffff803`40ef38c0 00000000`00000000 00000000`00000000 : nt!KiCallInterruptServiceRoutine+0xa5
fffff803`43a79fb0 fffff803`405f65b7 : ffffcd0f`f94dbc88 ffffcd0f`fc704338 00000000`c00000b5 01d6b9c6`0c945d0b : nt!KiInterruptSubDispatchNoLockNoEtw+0xfa
fffff803`43a6abe0 fffff803`5026d9e6 : ffffcd0f`fb056000 00000000`00000000 00000000`00000000 00000000`00000001 : nt!KiInterruptDispatchNoLockNoEtw+0x37
fffff803`43a6ad70 ffffcd0f`fb056000 : 00000000`00000000 00000000`00000000 00000000`00000001 fffff803`00000020 : nvlddmkm+0x20d9e6
fffff803`43a6ad78 00000000`00000000 : 00000000`00000000 00000000`00000001 fffff803`00000020 fffff803`43a6adb0 : 0xffffcd0f`fb056000
SYMBOL_NAME: nvlddmkm+20d9e6
MODULE_NAME: nvlddmkm
IMAGE_NAME: nvlddmkm.sys
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 20d9e6
FAILURE_BUCKET_ID: 0x133_ISR_nvlddmkm!unknown_function
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {f97493a5-ea2b-23ca-a808-8602773c2a86}
Followup: MachineOwner
---------