IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff800166e9a1e, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4936
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 74586
Key : Analysis.Memory.CommitPeak.Mb
Value: 83
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff800166e9a1e
WRITE_ADDRESS: fffff800170fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8001700f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8001700f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8001ba6b6d0 -- (.trap 0xfffff8001ba6b6d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=000004559e231800 rbx=0000000000000000 rcx=ffffe68f02b46000
rdx=0000045500000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff800166e9a1e rsp=fffff8001ba6b860 rbp=fffff8001ba6b960
r8=0000000000000000 r9=0000000000000000 r10=ffffe68f0b3afc88
r11=fffff8001ba6bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff800`166e9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff800`1ba6b588 fffff800`16805e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff800`1ba6b590 fffff800`16802169 : ffffab00`ae17b6f0 ffffe68f`08fcc6e8 ffffe68f`0b523000 fffff800`290bb717 : nt!KiBugCheckDispatch+0x69
fffff800`1ba6b6d0 fffff800`166e9a1e : fffff800`13857240 ffffe68f`02ce5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
fffff800`1ba6b860 fffff800`166e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
fffff800`1ba6b9d0 fffff800`167f7a0e : 00000000`00000000 fffff800`13854180 fffff800`17126600 ffffe68f`0dc16080 : nt!KiRetireDpcList+0x1f4
fffff800`1ba6bc60 00000000`00000000 : fffff800`1ba6c000 fffff800`1ba66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
0: kd> kb
# RetAddr : Args to Child : Call Site
00 fffff800`16805e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
01 fffff800`16802169 : ffffab00`ae17b6f0 ffffe68f`08fcc6e8 ffffe68f`0b523000 fffff800`290bb717 : nt!KiBugCheckDispatch+0x69
02 fffff800`166e9a1e : fffff800`13857240 ffffe68f`02ce5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
03 fffff800`166e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
04 fffff800`167f7a0e : 00000000`00000000 fffff800`13854180 fffff800`17126600 ffffe68f`0dc16080 : nt!KiRetireDpcList+0x1f4
05 00000000`00000000 : fffff800`1ba6c000 fffff800`1ba66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
0: kd> kv
# Child-SP RetAddr : Args to Child : Call Site
00 fffff800`1ba6b588 fffff800`16805e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
01 fffff800`1ba6b590 fffff800`16802169 : ffffab00`ae17b6f0 ffffe68f`08fcc6e8 ffffe68f`0b523000 fffff800`290bb717 : nt!KiBugCheckDispatch+0x69
02 fffff800`1ba6b6d0 fffff800`166e9a1e : fffff800`13857240 ffffe68f`02ce5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469 (TrapFrame @ fffff800`1ba6b6d0)
03 fffff800`1ba6b860 fffff800`166e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
04 fffff800`1ba6b9d0 fffff800`167f7a0e : 00000000`00000000 fffff800`13854180 fffff800`17126600 ffffe68f`0dc16080 : nt!KiRetireDpcList+0x1f4
05 fffff800`1ba6bc60 00000000`00000000 : fffff800`1ba6c000 fffff800`1ba66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
0: kd> .trap fffff800`1ba6b6d0
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=000004559e231800 rbx=0000000000000000 rcx=ffffe68f02b46000
rdx=0000045500000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff800166e9a1e rsp=fffff8001ba6b860 rbp=fffff8001ba6b960
r8=0000000000000000 r9=0000000000000000 r10=ffffe68f0b3afc88
r11=fffff8001ba6bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff800`166e9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
0: kd> kb
*** Stack trace for last set context - .thread/.cxr resets it
# RetAddr : Args to Child : Call Site
00 fffff800`166e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
01 fffff800`167f7a0e : 00000000`00000000 fffff800`13854180 fffff800`17126600 ffffe68f`0dc16080 : nt!KiRetireDpcList+0x1f4
02 00000000`00000000 : fffff800`1ba6c000 fffff800`1ba66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff80459ce9a1e, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4593
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 66280
Key : Analysis.Memory.CommitPeak.Mb
Value: 83
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff80459ce9a1e
WRITE_ADDRESS: fffff8045a6fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8045a60f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8045a60f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8045dc6b6d0 -- (.trap 0xfffff8045dc6b6d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=00001e35bc85306d rbx=0000000000000000 rcx=ffffa58d69735000
rdx=00001e3500000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80459ce9a1e rsp=fffff8045dc6b860 rbp=fffff8045dc6b960
r8=0000000000000000 r9=0000000000000000 r10=ffffa58d7219fc88
r11=fffff8045dc6bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff804`59ce9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff804`5dc6b588 fffff804`59e05e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff804`5dc6b590 fffff804`59e02169 : ffff8080`845c06f0 ffffa58d`707756e8 ffffa58d`77fc5000 fffff804`6a8ab717 : nt!KiBugCheckDispatch+0x69
fffff804`5dc6b6d0 fffff804`59ce9a1e : fffff804`559a2240 ffffa58d`698f5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
fffff804`5dc6b860 fffff804`59ce8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
fffff804`5dc6b9d0 fffff804`59df7a0e : 00000000`00000000 fffff804`5599f180 fffff804`5a726600 ffffa58d`700ad080 : nt!KiRetireDpcList+0x1f4
fffff804`5dc6bc60 00000000`00000000 : fffff804`5dc6c000 fffff804`5dc66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff802834e9a1e, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4359
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 49402
Key : Analysis.Memory.CommitPeak.Mb
Value: 83
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff802834e9a1e
WRITE_ADDRESS: fffff80283efa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff80283e0f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff80283e0f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8028706b6d0 -- (.trap 0xfffff8028706b6d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=00017b9d122a9cb4 rbx=0000000000000000 rcx=ffff968dfa135000
rdx=00017b9d00000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff802834e9a1e rsp=fffff8028706b860 rbp=fffff8028706b960
r8=0000000000000000 r9=0000000000000000 r10=ffff968e01a59f88
r11=fffff8028706bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff802`834e9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff802`8706b588 fffff802`83605e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff802`8706b590 fffff802`83602169 : 00000000`00000000 ffff968e`042176e8 00000000`00000000 fffff802`9390b978 : nt!KiBugCheckDispatch+0x69
fffff802`8706b6d0 fffff802`834e9a1e : fffff802`7ed7b240 ffff968d`fa2f5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
fffff802`8706b860 fffff802`834e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
fffff802`8706b9d0 fffff802`835f7a0e : 00000000`00000000 fffff802`7ed78180 fffff802`83f26600 ffff968e`068a1080 : nt!KiRetireDpcList+0x1f4
fffff802`8706bc60 00000000`00000000 : fffff802`8706c000 fffff802`87066000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff8016a4e9a1e, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 4812
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 80069
Key : Analysis.Memory.CommitPeak.Mb
Value: 83
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff8016a4e9a1e
WRITE_ADDRESS: fffff8016aefa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8016ae0f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8016ae0f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8016fe6b6d0 -- (.trap 0xfffff8016fe6b6d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=00000d01fe6c4b44 rbx=0000000000000000 rcx=ffffb186a8735000
rdx=00000d0100000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff8016a4e9a1e rsp=fffff8016fe6b860 rbp=fffff8016fe6b960
r8=0000000000000000 r9=0000000000000000 r10=ffffb186b0fd9f48
r11=fffff8016fe6bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff801`6a4e9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff801`6fe6b588 fffff801`6a605e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff801`6fe6b590 fffff801`6a602169 : ffff9681`dd4a46f0 ffffb186`af7986e8 ffffb186`b0f54000 fffff801`7c76b717 : nt!KiBugCheckDispatch+0x69
fffff801`6fe6b6d0 fffff801`6a4e9a1e : fffff801`67ca9240 ffffb186`a88f5000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
fffff801`6fe6b860 fffff801`6a4e8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
fffff801`6fe6b9d0 fffff801`6a5f7a0e : 00000000`00000000 fffff801`67ca6180 fffff801`6af26600 ffffb186`b1c48080 : nt!KiRetireDpcList+0x1f4
fffff801`6fe6bc60 00000000`00000000 : fffff801`6fe6c000 fffff801`6fe66000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
0: kd> lm
start end module name
ffffa68d`dee00000 ffffa68d`df0e2000 win32kbase (deferred)
ffffa68d`df0f0000 ffffa68d`df4a6000 win32kfull (deferred)
ffffa68d`df4c0000 ffffa68d`df55a000 win32k C (pdb symbols) C:\ProgramData\Dbg\sym\win32k.pdb\ED706A38659240A066E6FB19B994BAAA1\win32k.pdb
ffffa68d`df560000 ffffa68d`df5a8000 cdd (deferred)
fffff801`68b50000 fffff801`68b78000 mcupdate_AuthenticAMD (deferred)
fffff801`68b80000 fffff801`68b86000 hal (deferred)
fffff801`68b90000 fffff801`68b9b000 kd (deferred)
fffff801`68ba0000 fffff801`68bc7000 tm (deferred)
fffff801`68bd0000 fffff801`68c39000 CLFS (deferred)
fffff801`68c40000 fffff801`68c5a000 PSHED (deferred)
fffff801`68c60000 fffff801`68c6b000 BOOTVID (deferred)
fffff801`68c70000 fffff801`68d83000 clipsp (deferred)
fffff801`68d90000 fffff801`68dff000 FLTMGR (deferred)
fffff801`68e00000 fffff801`68e29000 ksecdd (deferred)
fffff801`68e30000 fffff801`68e92000 msrpc (deferred)
fffff801`68ea0000 fffff801`68eae000 cmimcext (deferred)
fffff801`68eb0000 fffff801`68ec1000 werkernel (deferred)
fffff801`68ed0000 fffff801`68edc000 ntosext (deferred)
fffff801`68ee0000 fffff801`68ef3000 WDFLDR (deferred)
fffff801`68f00000 fffff801`68f0f000 SleepStudyHelper (deferred)
fffff801`68f10000 fffff801`68f21000 WppRecorder (deferred)
fffff801`68f30000 fffff801`68f4a000 SgrmAgent (deferred)
fffff801`6a200000 fffff801`6b246000 nt (pdb symbols) C:\ProgramData\Dbg\sym\ntkrnlmp.pdb\641F55C592201DCC4F59FACC72EA54DA1\ntkrnlmp.pdb
fffff801`6e400000 fffff801`6e4e3000 CI (deferred)
fffff801`6e4f0000 fffff801`6e5a7000 cng (deferred)
fffff801`6e5b0000 fffff801`6e681000 Wdf01000 (deferred)
fffff801`6e690000 fffff801`6e6b6000 acpiex (deferred)
fffff801`6e6c0000 fffff801`6e70b000 mssecflt (deferred)
fffff801`6e710000 fffff801`6e7dc000 ACPI (deferred)
fffff801`6e7e0000 fffff801`6e7ec000 WMILIB (deferred)
fffff801`6e810000 fffff801`6e87b000 intelpep (deferred)
fffff801`6e880000 fffff801`6e897000 WindowsTrustedRT (deferred)
fffff801`6e8a0000 fffff801`6e8ab000 IntelTA (deferred)
fffff801`6e8b0000 fffff801`6e8bb000 WindowsTrustedRTProxy (deferred)
fffff801`6e8c0000 fffff801`6e8d4000 pcw (deferred)
fffff801`6e8e0000 fffff801`6e8eb000 msisadrv (deferred)
fffff801`6e8f0000 fffff801`6e968000 pci (deferred)
fffff801`6e970000 fffff801`6e985000 vdrvroot (deferred)
fffff801`6e990000 fffff801`6e9a6000 amdkmpfd (deferred)
fffff801`6e9b0000 fffff801`6e9df000 pdc (deferred)
fffff801`6e9e0000 fffff801`6e9f9000 CEA (deferred)
fffff801`6ea00000 fffff801`6ea31000 partmgr (deferred)
fffff801`6ea40000 fffff801`6eaea000 spaceport (deferred)
fffff801`6eaf0000 fffff801`6eb09000 volmgr (deferred)
fffff801`6eb10000 fffff801`6eb73000 volmgrx (deferred)
fffff801`6eb80000 fffff801`6eb9e000 mountmgr (deferred)
fffff801`6eba0000 fffff801`6ebd2000 storahci (deferred)
fffff801`6ebe0000 fffff801`6ebfc000 EhStorClass (deferred)
fffff801`6ec00000 fffff801`6ecb0000 storport (deferred)
fffff801`6ecc0000 fffff801`6ecda000 fileinfo (deferred)
fffff801`6ece0000 fffff801`6ed20000 Wof (deferred)
fffff801`6ed30000 fffff801`6ed9c000 WdFilter (deferred)
fffff801`6eda0000 fffff801`6edad000 Fs_Rec (deferred)
fffff801`6edb0000 fffff801`6ef1f000 ndis (deferred)
fffff801`6ef20000 fffff801`6efb8000 NETIO (deferred)
fffff801`6efc0000 fffff801`6eff2000 ksecpkg (deferred)
fffff801`6f000000 fffff801`6f2d9000 Ntfs (deferred)
fffff801`6f2e0000 fffff801`6f301000 amdpsp (deferred)
fffff801`6f310000 fffff801`6f5fc000 tcpip (deferred)
fffff801`6f600000 fffff801`6f67f000 fwpkclnt (deferred)
fffff801`6f680000 fffff801`6f6b0000 wfplwfs (deferred)
fffff801`6f6c0000 fffff801`6f789000 fvevol (deferred)
fffff801`6f790000 fffff801`6f79b000 volume (deferred)
fffff801`6f7a0000 fffff801`6f80d000 volsnap (deferred)
fffff801`6f810000 fffff801`6f860000 rdyboost (deferred)
fffff801`6f870000 fffff801`6f896000 mup (deferred)
fffff801`6f8a0000 fffff801`6f8b2000 iorate (deferred)
fffff801`6f8e0000 fffff801`6f8fc000 disk (deferred)
fffff801`6f900000 fffff801`6f96c000 CLASSPNP (deferred)
fffff801`760a0000 fffff801`760be000 crashdmp (deferred)
fffff801`76800000 fffff801`76830000 cdrom (deferred)
fffff801`76840000 fffff801`76855000 filecrypt (deferred)
fffff801`76860000 fffff801`7686e000 tbs (deferred)
fffff801`76870000 fffff801`7687a000 Null (deferred)
fffff801`76880000 fffff801`7688a000 Beep (deferred)
fffff801`76890000 fffff801`76dc7000 vgk (deferred)
fffff801`76e00000 fffff801`76e10000 TDI (deferred)
fffff801`76e20000 fffff801`76e7c000 netbt (deferred)
fffff801`76e80000 fffff801`76e93000 afunix (deferred)
fffff801`76ea0000 fffff801`76f43000 afd (deferred)
fffff801`76f50000 fffff801`76f6a000 vwififlt (deferred)
fffff801`76f70000 fffff801`76f9b000 pacer (deferred)
fffff801`76fa0000 fffff801`76fb4000 ndiscap (deferred)
fffff801`76fc0000 fffff801`76fd4000 netbios (deferred)
fffff801`76fe0000 fffff801`77081000 Vid (deferred)
fffff801`77090000 fffff801`770b1000 winhvr (deferred)
fffff801`770c0000 fffff801`7713b000 rdbss (deferred)
fffff801`77140000 fffff801`771d4000 csc (deferred)
fffff801`771e0000 fffff801`771f2000 nsiproxy (deferred)
fffff801`77200000 fffff801`7720e000 npsvctrig (deferred)
fffff801`77210000 fffff801`77220000 mssmbios (deferred)
fffff801`77230000 fffff801`7723a000 gpuenergydrv (deferred)
fffff801`77240000 fffff801`77248000 GLCKIO2 (deferred)
fffff801`77250000 fffff801`77257000 ene (deferred)
fffff801`77260000 fffff801`7728c000 dfsc (deferred)
fffff801`772b0000 fffff801`7731c000 fastfat (deferred)
fffff801`77320000 fffff801`77337000 bam (deferred)
fffff801`77340000 fffff801`77349000 AsIO2 (deferred)
fffff801`77350000 fffff801`77359000 AsUpIO (deferred)
fffff801`77360000 fffff801`77366000 AsIO (deferred)
fffff801`77370000 fffff801`773be000 ahcache (deferred)
fffff801`773c0000 fffff801`773d2000 CompositeBus (deferred)
fffff801`773e0000 fffff801`773ed000 kdnic (deferred)
fffff801`773f0000 fffff801`77405000 umbus (deferred)
fffff801`77410000 fffff801`77411f80 AiCharger (deferred)
fffff801`77420000 fffff801`774b8000 USBXHCI (deferred)
fffff801`774c0000 fffff801`77504000 ucx01000 (deferred)
fffff801`77510000 fffff801`77626000 rt640x64 (deferred)
fffff801`77630000 fffff801`776c2000 atikmpag (deferred)
fffff801`776d0000 fffff801`777a6000 peauth (deferred)
fffff801`777b0000 fffff801`77877000 srv2 (deferred)
fffff801`77880000 fffff801`778a1000 raspptp (deferred)
fffff801`778b0000 fffff801`778cc000 raspppoe (deferred)
fffff801`778d0000 fffff801`7790a000 ndiswan (deferred)
fffff801`77910000 fffff801`77926000 WdNisDrv (deferred)
fffff801`77930000 fffff801`77943000 condrv (deferred)
fffff801`77d50000 fffff801`780f4000 dxgkrnl (deferred)
fffff801`78100000 fffff801`78118000 watchdog (deferred)
fffff801`78120000 fffff801`78136000 BasicDisplay (deferred)
fffff801`78140000 fffff801`78151000 BasicRender (deferred)
fffff801`78160000 fffff801`7817c000 Npfs (deferred)
fffff801`78180000 fffff801`78191000 Msfs (deferred)
fffff801`781a0000 fffff801`781bb000 CimFS (deferred)
fffff801`781c0000 fffff801`781e2000 tdx (deferred)
fffff801`78a00000 fffff801`78a11000 kbdhid (deferred)
fffff801`78a20000 fffff801`78a34000 kbdclass (deferred)
fffff801`78a40000 fffff801`78a50000 mouhid (deferred)
fffff801`78a60000 fffff801`78a73000 mouclass (deferred)
fffff801`78a90000 fffff801`78a9e000 dump_diskdump (deferred)
fffff801`78ae0000 fffff801`78b12000 dump_storahci (deferred)
fffff801`78b40000 fffff801`78b5d000 dump_dumpfve (deferred)
fffff801`78b60000 fffff801`78c41000 dxgmms2 (deferred)
fffff801`78c50000 fffff801`78c6b000 monitor (deferred)
fffff801`78c70000 fffff801`78c84000 qwavedrv (deferred)
fffff801`78d10000 fffff801`78d39000 luafv (deferred)
fffff801`78d40000 fffff801`78d76000 wcifs (deferred)
fffff801`78d80000 fffff801`78e00000 cldflt (deferred)
fffff801`78e10000 fffff801`78e2a000 storqosflt (deferred)
fffff801`78e30000 fffff801`78e57000 bindflt (deferred)
fffff801`78e60000 fffff801`78e78000 mslldp (deferred)
fffff801`78e80000 fffff801`78e98000 lltdio (deferred)
fffff801`78ea0000 fffff801`78ebb000 rspndr (deferred)
fffff801`78ec0000 fffff801`78edd000 wanarp (deferred)
fffff801`78ee0000 fffff801`78f36000 msquic (deferred)
fffff801`78f40000 fffff801`790c6000 HTTP (deferred)
fffff801`790d0000 fffff801`790f5000 bowser (deferred)
fffff801`79100000 fffff801`7911a000 mpsdrv (deferred)
fffff801`79120000 fffff801`79165000 mrxsmb20 (deferred)
fffff801`79170000 fffff801`791a4000 AMDRyzenMasterDriver (deferred)
fffff801`791b0000 fffff801`7983c000 RTKVHD64 (deferred)
fffff801`79850000 fffff801`79883000 usbccgp (deferred)
fffff801`79890000 fffff801`798e2000 srvnet (deferred)
fffff801`798f0000 fffff801`79904000 mmcss (deferred)
fffff801`79910000 fffff801`7991f000 ndistapi (deferred)
fffff801`79920000 fffff801`79931000 UAExt (deferred)
fffff801`79940000 fffff801`79977000 usbaudio (deferred)
fffff801`79980000 fffff801`79992000 hidusb (deferred)
fffff801`799a0000 fffff801`799df000 HIDCLASS (deferred)
fffff801`799e0000 fffff801`799f3000 HIDPARSE (deferred)
fffff801`7c200000 fffff801`7c221000 drmk (deferred)
fffff801`7c230000 fffff801`7c2a6000 ks (deferred)
fffff801`7c2b0000 fffff801`7c2ba000 AMDPCIDev (deferred)
fffff801`7c2c0000 fffff801`7c2dc000 serial (deferred)
fffff801`7c2e0000 fffff801`7c2ef000 serenum (deferred)
fffff801`7c2f0000 fffff801`7c2fd000 amdgpio2 (deferred)
fffff801`7c300000 fffff801`7c332000 msgpioclx (deferred)
fffff801`7c340000 fffff801`7c34c000 wmiacpi (deferred)
fffff801`7c350000 fffff801`7c38b000 amdppm (deferred)
fffff801`7c390000 fffff801`7c39a000 amdgpio3 (deferred)
fffff801`7c3a0000 fffff801`7c3ae000 UEFI (deferred)
fffff801`7c3b0000 fffff801`7c3bd000 NdisVirtualBus (deferred)
fffff801`7c3c0000 fffff801`7c3cc000 swenum (deferred)
fffff801`7c3d0000 fffff801`7c3de000 rdpbus (deferred)
fffff801`7c3e0000 fffff801`7c483000 UsbHub3 (deferred)
fffff801`7c490000 fffff801`7c49e000 USBD (deferred)
fffff801`7c4a0000 fffff801`7c4bd000 AtihdWT6 (deferred)
fffff801`7c4c0000 fffff801`7c4cf000 ksthunk (deferred)
fffff801`7c4d0000 fffff801`7c563000 mrxsmb (deferred)
fffff801`7c570000 fffff801`7c597000 Ndu (deferred)
fffff801`7c5a0000 fffff801`7c5b5000 tcpipreg (deferred)
fffff801`7c5c0000 fffff801`7c5dc000 rassstp (deferred)
fffff801`7c5e0000 fffff801`7c5fd000 NDProxy (deferred)
fffff801`7c600000 fffff801`7c627000 AgileVpn (deferred)
fffff801`7c630000 fffff801`7c651000 rasl2tp (deferred)
fffff801`7c660000 fffff801`7c669000 IOMap64 (deferred)
fffff801`7c670000 fffff801`80556000 atikmdag (deferred)
fffff801`80560000 fffff801`80585000 HDAudBus (deferred)
fffff801`80590000 fffff801`805f6000 portcls (deferred)
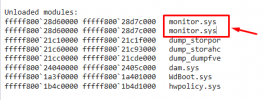
Unloaded modules:
fffff801`768b0000 fffff801`76df5000 vgk.sys
fffff801`79840000 fffff801`7984e000 AppleLowerFi
fffff801`78d00000 fffff801`78d0f000 WpdUpFltr.sy
fffff801`78ca0000 fffff801`78cf5000 WUDFRd.sys
fffff801`78c70000 fffff801`78c91000 WinUSB.SYS
fffff801`760d0000 fffff801`760df000 dump_storpor
fffff801`76120000 fffff801`76153000 dump_storahc
fffff801`76180000 fffff801`7619e000 dump_dumpfve
fffff801`79890000 fffff801`798b1000 WinUSB.SYS
fffff801`798c0000 fffff801`79915000 WUDFRd.sys
fffff801`77290000 fffff801`772ac000 dam.sys
fffff801`6e7f0000 fffff801`6e801000 WdBoot.sys
fffff801`6f8c0000 fffff801`6f8d1000 hwpolicy.sys
0: kd> lmDvmmonitor
Browse full module list
start end module name
fffff801`78c50000 fffff801`78c6b000 monitor (deferred)
Mapped memory image file: C:\ProgramData\Dbg\sym\monitor.sys\1CD682D71b000\monitor.sys
Image path: \SystemRoot\System32\drivers\monitor.sys
Image name: monitor.sys
Browse all global symbols functions data
Image was built with /Brepro flag.
Timestamp: 1CD682D7 (This is a reproducible build file hash, not a timestamp)
CheckSum: 0001751B
ImageSize: 0001B000
File version: 10.0.19041.508
Product version: 10.0.19041.508
File flags: 0 (Mask 3F)
File OS: 40004 NT Win32
File type: 3.7 Driver
File date: 00000000.00000000
Translations: 0409.04b0
Information from resource tables:
CompanyName: Microsoft Corporation
ProductName: Microsoft® Windows® Operating System
InternalName: monitor.sys
OriginalFilename: monitor.sys
ProductVersion: 10.0.19041.508
FileVersion: 10.0.19041.508 (WinBuild.160101.0800)
FileDescription: Monitor Driver
LegalCopyright: © Microsoft Corporation. All rights reserved.
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff80203ae9a1e, address which referenced memory
Debugging Details:
------------------
*** WARNING: Unable to verify checksum for win32k.sys
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 5218
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 77906
Key : Analysis.Memory.CommitPeak.Mb
Value: 85
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff80203ae9a1e
WRITE_ADDRESS: fffff802044fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8020440f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8020440f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: System
TRAP_FRAME: fffff8020946b6d0 -- (.trap 0xfffff8020946b6d0)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=0000096746f53086 rbx=0000000000000000 rcx=ffffd78eccf46000
rdx=0000096700000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80203ae9a1e rsp=fffff8020946b860 rbp=fffff8020946b960
r8=0000000000000000 r9=0000000000000000 r10=ffffd78ecffbbe38
r11=fffff8020946bb10 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff802`03ae9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff802`0946b588 fffff802`03c05e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff802`0946b590 fffff802`03c02169 : ffff9480`3c2fe1f0 ffffd78e`cffec6e8 ffffd78e`d68a6000 fffff802`1929bd87 : nt!KiBugCheckDispatch+0x69
fffff802`0946b6d0 fffff802`03ae9a1e : fffff802`00fdf240 ffffd78e`ce0f1000 00000000`00000000 00000000`00000002 : nt!KiPageFault+0x469
fffff802`0946b860 fffff802`03ae8d24 : 00000000`00000000 00000000`00000000 00000000`00140001 00000000`00000000 : nt!KiExecuteAllDpcs+0x2ee
fffff802`0946b9d0 fffff802`03bf7a0e : 00000000`00000000 fffff802`00fdc180 fffff802`04526600 ffffd78e`d83b7080 : nt!KiRetireDpcList+0x1f4
fffff802`0946bc60 00000000`00000000 : fffff802`0946c000 fffff802`09466000 00000000`00000000 00000000`00000000 : nt!KiIdleLoop+0x9e
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff8001f4e9a1e, address which referenced memory
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 6296
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 71698
Key : Analysis.Memory.CommitPeak.Mb
Value: 93
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff8001f4e9a1e
WRITE_ADDRESS: fffff8001fefa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8001fe0f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8001fe0f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: AMDRSServ.exe
DPC_STACK_BASE: FFFFF80022C72FB0
TRAP_FRAME: ffff9cad82e97010 -- (.trap 0xffff9cad82e97010)
Unable to read trap frame at ffff9cad`82e97010
STACK_TEXT:
fffff800`22c728d8 fffff800`1f605e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff800`22c728e0 fffff800`1f602169 : 000022f5`cb0d972c 00000000`00000002 ffffb08d`6d902000 fffff800`2fc59f37 : nt!KiBugCheckDispatch+0x69
fffff800`22c72a20 fffff800`1f4e9a1e : fffff800`1a7b9240 ffffb08d`650f8000 fffff800`22c72e70 fffff800`00000002 : nt!KiPageFault+0x469
fffff800`22c72bb0 fffff800`1f4e8d24 : fffff800`1a7b6180 00000000`00000000 00000000`00000002 00000000`00000004 : nt!KiExecuteAllDpcs+0x2ee
fffff800`22c72d20 fffff800`1f5faee5 : 00000000`00000000 fffff800`1a7b6180 ffff9f80`60cfe140 00000000`00000000 : nt!KiRetireDpcList+0x1f4
fffff800`22c72fb0 fffff800`1f5facd0 : fffff800`1f5eff90 fffff800`1f43f03a ffffb08d`6f192000 00000000`ffffffff : nt!KxRetireDpcList+0x5
ffffc109`a2253850 fffff800`1f5fa585 : 00000000`00000000 fffff800`1f5f5a11 00000000`00300d68 00000000`00000000 : nt!KiDispatchInterruptContinue
ffffc109`a2253880 fffff800`1f5f5a11 : 00000000`00300d68 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiDpcInterruptBypass+0x25
ffffc109`a2253890 ffff9c86`ab6656d4 : 00000000`00300d68 ffffef8b`09542b92 ffff9cad`82e97010 ffffc109`a2253a30 : nt!KiInterruptDispatch+0xb1
ffffc109`a2253a20 ffff9c86`acb6473f : 000001c0`7236dc90 00000000`00300d68 ffffc109`a2253b80 ffff9c86`acafb28a : win32kbase!ValidateHwnd+0x4
ffffc109`a2253a50 ffff9c86`abb75bf1 : ffffb08d`6d7e8300 00000000`00000001 00000000`00000000 000001c0`4f023e70 : win32kfull!NtUserGetClassName+0x4f
ffffc109`a2253ad0 fffff800`1f6058b8 : ffffb08d`6d7e8300 00000000`00000000 00000000`00000000 00000000`00000001 : win32k!NtUserGetClassName+0x15
ffffc109`a2253b00 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiSystemServiceCopyEnd+0x28
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
IRQL_NOT_LESS_OR_EQUAL (a)
An attempt was made to access a pageable (or completely invalid) address at an
interrupt request level (IRQL) that is too high. This is usually
caused by drivers using improper addresses.
If a kernel debugger is available get the stack backtrace.
Arguments:
Arg1: 0000000000000020, memory referenced
Arg2: 0000000000000002, IRQL
Arg3: 0000000000000001, bitfield :
bit 0 : value 0 = read operation, 1 = write operation
bit 3 : value 0 = not an execute operation, 1 = execute operation (only on chips which support this level of status)
Arg4: fffff80142ce9a1e, address which referenced memory
Debugging Details:
------------------
KEY_VALUES_STRING: 1
Key : Analysis.CPU.mSec
Value: 5218
Key : Analysis.DebugAnalysisProvider.CPP
Value: Create: 8007007e on DESKTOP-1IBQR0U
Key : Analysis.DebugData
Value: CreateObject
Key : Analysis.DebugModel
Value: CreateObject
Key : Analysis.Elapsed.mSec
Value: 74598
Key : Analysis.Memory.CommitPeak.Mb
Value: 75
Key : Analysis.System
Value: CreateObject
Key : WER.OS.Branch
Value: vb_release
Key : WER.OS.Timestamp
Value: 2019-12-06T14:06:00Z
Key : WER.OS.Version
Value: 10.0.19041.1
ADDITIONAL_XML: 1
OS_BUILD_LAYERS: 1
BUGCHECK_CODE: a
BUGCHECK_P1: 20
BUGCHECK_P2: 2
BUGCHECK_P3: 1
BUGCHECK_P4: fffff80142ce9a1e
WRITE_ADDRESS: fffff801436fa390: Unable to get MiVisibleState
Unable to get NonPagedPoolStart
Unable to get NonPagedPoolEnd
Unable to get PagedPoolStart
Unable to get PagedPoolEnd
fffff8014360f2e0: Unable to get Flags value from nt!KdVersionBlock
fffff8014360f2e0: Unable to get Flags value from nt!KdVersionBlock
unable to get nt!MmSpecialPagesInUse
0000000000000020
BLACKBOXBSD: 1 (!blackboxbsd)
BLACKBOXNTFS: 1 (!blackboxntfs)
BLACKBOXPNP: 1 (!blackboxpnp)
BLACKBOXWINLOGON: 1
CUSTOMER_CRASH_COUNT: 1
PROCESS_NAME: League of Legends.exe
DPC_STACK_BASE: FFFFF80145872FB0
TRAP_FRAME: fffff80145872a20 -- (.trap 0xfffff80145872a20)
NOTE: The trap frame does not contain all registers.
Some register values may be zeroed or incorrect.
rax=00004a83da5af6e4 rbx=0000000000000000 rcx=ffff978fb7935000
rdx=00004a8300000000 rsi=0000000000000000 rdi=0000000000000000
rip=fffff80142ce9a1e rsp=fffff80145872bb0 rbp=fffff80145872cb0
r8=0000000000000000 r9=0000000000000000 r10=ffff978fc11ecf88
r11=fffff80145872e60 r12=0000000000000000 r13=0000000000000000
r14=0000000000000000 r15=0000000000000000
iopl=0 nv up ei ng nz ac po cy
nt!KiExecuteAllDpcs+0x2ee:
fffff801`42ce9a1e 49894720 mov qword ptr [r15+20h],rax ds:00000000`00000020=????????????????
Resetting default scope
STACK_TEXT:
fffff801`458728d8 fffff801`42e05e69 : 00000000`0000000a 00000000`00000020 00000000`00000002 00000000`00000001 : nt!KeBugCheckEx
fffff801`458728e0 fffff801`42e02169 : 00004a83`da570c24 00000000`00000000 ffff978f`c1002000 fffff801`526e9c37 : nt!KiBugCheckDispatch+0x69
fffff801`45872a20 fffff801`42ce9a1e : fffff801`3d759240 ffff978f`b7af7000 fffff801`45872e70 fffff801`00000002 : nt!KiPageFault+0x469
fffff801`45872bb0 fffff801`42ce8d24 : fffff801`3d756180 00000000`00000000 00000000`00000002 00000000`00000004 : nt!KiExecuteAllDpcs+0x2ee
fffff801`45872d20 fffff801`42dfaee5 : 00000000`00000000 fffff801`3d756180 ffff8081`42834640 00000000`7ffea000 : nt!KiRetireDpcList+0x1f4
fffff801`45872fb0 fffff801`42dfacd0 : fffff801`42deff90 fffff801`42c3f03a ffff978f`c8ba9080 00000000`76359560 : nt!KxRetireDpcList+0x5
ffffe80b`8b4d8ac0 fffff801`42dfa585 : 00000000`7ffea000 fffff801`42df5a11 00000000`0000e383 ffff978f`c80cd080 : nt!KiDispatchInterruptContinue
ffffe80b`8b4d8af0 fffff801`42df5a11 : 00000000`0000e383 ffff978f`c80cd080 00000000`00000000 00000000`00000000 : nt!KiDpcInterruptBypass+0x25
ffffe80b`8b4d8b00 00000000`00000000 : 00000000`00000000 00000000`00000000 00000000`00000000 00000000`00000000 : nt!KiInterruptDispatch+0xb1
SYMBOL_NAME: nt!KiExecuteAllDpcs+2ee
MODULE_NAME: nt
IMAGE_NAME: ntkrnlmp.exe
IMAGE_VERSION: 10.0.19041.508
STACK_COMMAND: .thread ; .cxr ; kb
BUCKET_ID_FUNC_OFFSET: 2ee
FAILURE_BUCKET_ID: AV_nt!KiExecuteAllDpcs
OS_VERSION: 10.0.19041.1
BUILDLAB_STR: vb_release
OSPLATFORM_TYPE: x64
OSNAME: Windows 10
FAILURE_ID_HASH: {b88a28a0-fcde-99e9-6174-619833d00ab9}
Followup: MachineOwner
---------
 .
.